Welcome everybody! I hope you wonderful people are doing great and street to Ethical Hacking is going straight. I believe past September and this Hacktober is a standout amongst other months in my hacking career. Learned a couple of more things and cleared some of my misguided concepts. Joined CoderStack as a tutor to guide other individuals about the risk and significance of Cyber Security and Ethical Hacking.
How magnificent it's hard when somebody says "I Hacked Google". Indeed I hacked google. I am not saying I bargained for Google security but rather there was a security misconfiguration in one of its acquisitions which can be used to pick up unauthorized access to users information.
When I took a step in Cyber Security I wished to highlight in Google the rundown of security people and groups who actually helped Google for finding and revealing security vulnerabilities to Google and it's acquisitions. Genuine joy is when dreams work out as expected. A day I got highlighted, let me share a story with you, Hang tight!
FameBit is an acquisition of google which is an online marketplace that connects YouTubers with brands that are interested in advertising their products and services. This provides creators with an opportunity to earn money with their content by partnering with brands that are relevant to their audience.
Noted FameBit to my sticky notes to play out a security test on it later. As I kicked time I started testing it and in the wake of playing with its requests, I established some security flaws which were related to Session Management and Authentication. We should brief them minimally more.
**Session Management: **In this security vulnerability, I have figured out how to log in any individual to the attacker account in this manner, when any user logged in to the attacker account, the attacker can see the user activity inside the attacker account. For example, sensitive information and more. The issue depends on registration confirmation together with the password reset.
*Steps to Replicate: *
- Attacker registered his account.
- Account registration confirmation mail will be sent to the attacker's email.
- Attackers send the registration confirmation link to the user.
- As the user taps the link he will automatically sign in to the attacker's account.
- All done, the user will surmise that he is in his own account but actually he is in the attacker's account.
I observed that the password key creation was not enforced on the registration form and this will cause the issue on both endpoints (enrollment and reset password).
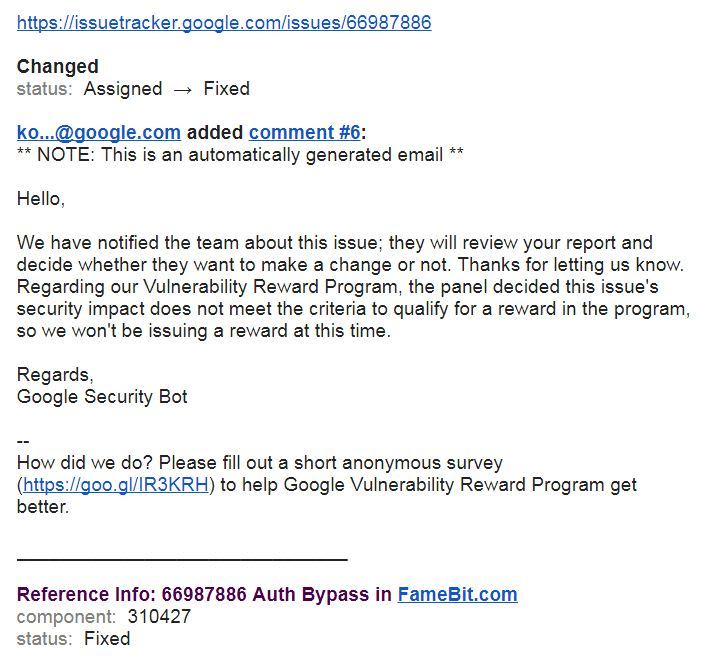
I composed a point by point report and provided it to the Google security team and they triaged it and began taking a look at it. It took half a month to decide and move over a fix. Following fifteen days, I got a mail from google that they fixed the security issue.
After that, I visited my Google VRP profile with a lot of expectations and then I noticed that I've been included on Google Security researchers hall of fame page. I truly commend that minute. This celebration can be considerably greater if the report is qualified for a bug bounty. Yet I have no stress. I'll attempt better fortunes next time :)
Thanks for taking the time, I truly value that. I look forward to seeing you there again soon enough. I require recommendations from you wonderful people.



Top comments (0)