This is a learner post so if anything needs to be corrected or updated, kindly comment. will be helpful to know !.
When our application contains more than one container. For instance a food application might need a frontend, backend, databases based container.
We need to exchange information between containers. we need a network to carry out crucial data between containers. communication can be one to one or many to one.
How do they manage ?
Network Drivers!!
- Piece of software , that handles container networking. created by network command.
- invoking network inside the cluster or host
- docker itself uses these network drivers to communicate with other container. So it provide native network driver. We can even use 3rd party drivers for specific use case.
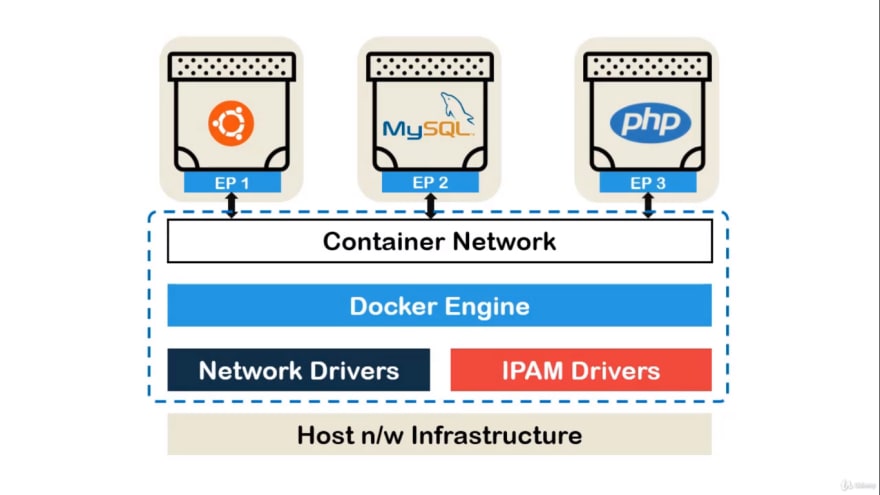
Container Networking model:
Host N/W infrastructure: includes software and hardware infrastructure Wifi , ethernet and host kernel network stack.
IPAM manages IP address within context
Docker Engine creates Individual network object. user created and default container network.
If a container contains more than one network , it will have more than one endpoints and different set of IP address.
When its single host implementation, scopes are limited.
Within the same scope, if two containers are connected to same network it can communicate via DNS where container names can be used instead of IP. These informations are provided by IPAM. Then the driver and IPAM convert the request as host supported network packets. We need to make sure the containers communicate outside, if not simple apt-get command won't execute.
Types of Native Network ?
Host Network:
The container is not isolated from the docker host. If you run container that binds with ports 80 and if we use host networking then the container is available in port 80 of host IP address.
This is used for handling large number of ports, where we require NTA or proxy.
But this type of network is available only for Linux, not for windows or Mac.
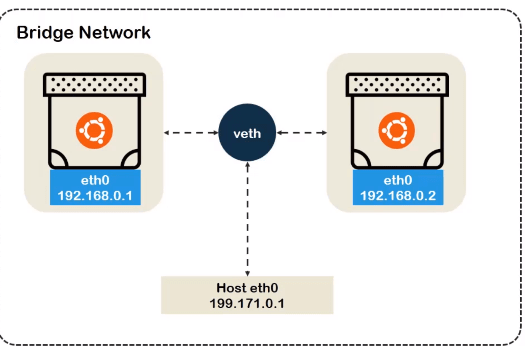
Bridge Network:
- Default for docker container. If we don't specify any network it will assign to default bridge network.
- This bridge network connect containers with virtual ethernet and communicates to host via this ethernet. Container will have different IPs as the host is isolated from the container. The container and host communication within only same bridge scope.
- We can provide IP range and subnet mask for the bridge network, or the IPAM will manage the ip address for us, we can ping the address provided in the virtual bridge.
Overlay Network:
This does not apply for single host infrastructure. This applies where there is more than one docker host daemon or containers. Hence keeping track of container Ip is not enough , as we need to communicate with container and host, so we will maintain 2 layer of information.
overlay information - Ingress:
connect the data and control of the source and destination Container IP. Docker Swarm data and network traffic is handled by ingress network. Hence use this information by default
underlay information- docker_gwbridge:
Data regarding the source and destination host IP. Docker Swarn , it is bridge network which connects the individual Docker daemon to the other daemons.
MacVlan Network:(virtual local area network) It is a virtualisation , where we have multiple mac of a physical interface which has its own ip address. This type can be used for application whch monitors the network traffice where it is directly connected to physical interface.
Advantage of using macvlan is performence is better than overlay and does not linux bridge*.
things to be noted before using mcvlan
- unintentional damange to the physical network since it is directly connect.
- able to handle "promiscuous mode" where one physical network is assigned to multiple mac address.
- if your application works in both overlay and bridge, then they should be long term.
IpVlan Network: same as macvlan but endpoint has same mac address,has 2 mode l2 and l3. L2 where end points has same mac address different ip address , L3 packets are rounted between endpoints.
uses of Ipvlan
ipvlan should be used in cases where some switches restrict the maximum number of mac address per physical port due to port security configuration.
Linux bridge* - it is like a regular hardware switch with learning and also supports protocols like STP for loop prevention. Here VMs or Containers will connect to bridge and bridge will connect to outside world. For external connectivity, we would need to use NAT.


Top comments (0)