ACloudGuru ElastiCache Challenge
I decided to take this challenge when I saw that they released it, because I am planning on writing my AWS Developer Associate Certification soon and wanted some practical projects to work on while preparing for the exam. I recently build my NextJS portfolio website which I am hosting as a static website on AWS S3 and then using CloudFront as my distribution and HTTPS provider pointing to my Static website. Then by using AWS Lambda and DynamoDB, I created a function to increment my page visits every time the website gets viewed. I wanted more exposure to CloudFormation templates and decided to do this challenges in CloudFormation templates instead of the AWS console or CLI.
CloudFormation Template
I started with the parameters, to have some flexibility and to focus on referencing them in the template. I decided for testing purposes to use my EC2 keypair and the master database username as parameters. I wanted to keep the master database password a bit secure, so I used SSM secure string to keep my master password. There are many ways one can approach this. In this challenge I wanted to test and see how I could reference a parameter coming from somewhere else in AWS instead of CloudFormation.

Next I started working on the Security Groups, I allowed HTTP and the flask port to my EC2 server to be able to browse to my app from my local computer. Then with the RDS and ElastiCache security groups I referenced the SG of my EC2 server, so that only my EC2 server can communicate to those services.
 The next part creates a RDS PostgreSQL database which will be in the free tier if you keep the setup as is. Then for the master password I decided to use SSM SecureString to store my Database password, encryption will be handled by AWS KMS, but I wanted to test out as well how to incorporate the SSM store within my template, as there are a few ways you can configure this for secure password storage. For the MasterUsername we the intrinsic function !Ref which returns the value of our RDSDatabaseUsername parameter.
The next part creates a RDS PostgreSQL database which will be in the free tier if you keep the setup as is. Then for the master password I decided to use SSM SecureString to store my Database password, encryption will be handled by AWS KMS, but I wanted to test out as well how to incorporate the SSM store within my template, as there are a few ways you can configure this for secure password storage. For the MasterUsername we the intrinsic function !Ref which returns the value of our RDSDatabaseUsername parameter.

The next part we will have a look at our EC2 configuration. It is also setup to be within the free tier in AWS. We also use the intrinsic function !Ref to get our KeyName value and also our Security Group for the EC2. In the user data section we use a bootstrap script which will only run once when our EC2 gets created, this is to setup the EC2 the way we need it to run without going in after and setup everything manually. You can basically setup anything on the UserData section to config your EC2 the way you need it to be.

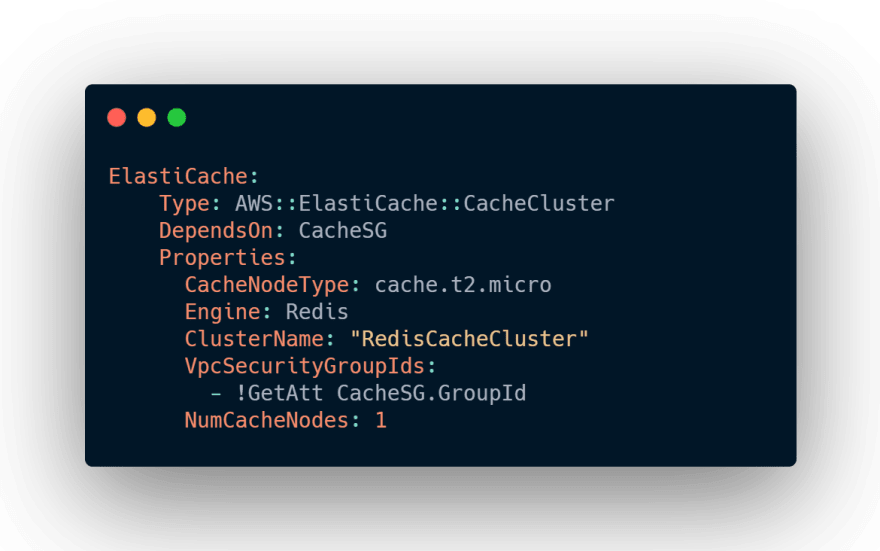
Here we will create our Redis ElastiCache which we will use in our Flask app to use to cache our results. This will also be within the free tier of AWS.
The next section we just output our Public DNS name of our EC2 and then as well our URL of our RDS PostgreSQL database that we can use.

Flask Application
Now that our service on AWS is up and configured, we can edit our Flask app so that we check if the results are cached in our ElastiCache and if it is it will return the cached result, which will return a response quickly and if it doesn't exist in the cache then we query the RDS server and will return a slower response.
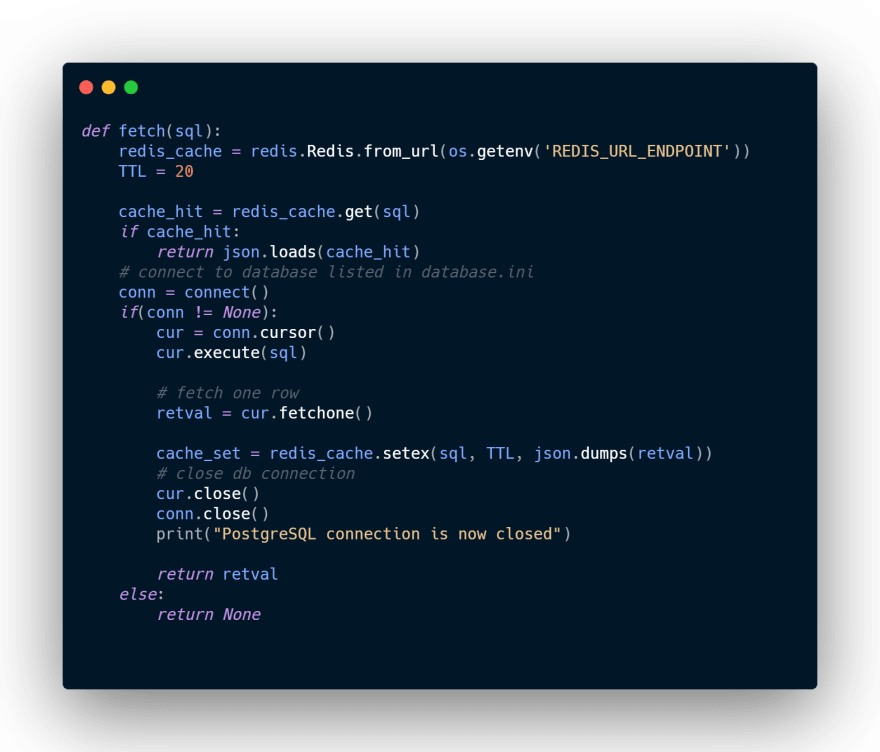
Here we visit our web app for the first time which would have no results in the ElastiCache and would need to query our RDS database and will return a slower response.

Now that result will be saved in our cache, which means if we refresh our page again the next few times we will have a very quick response time and quick page load.
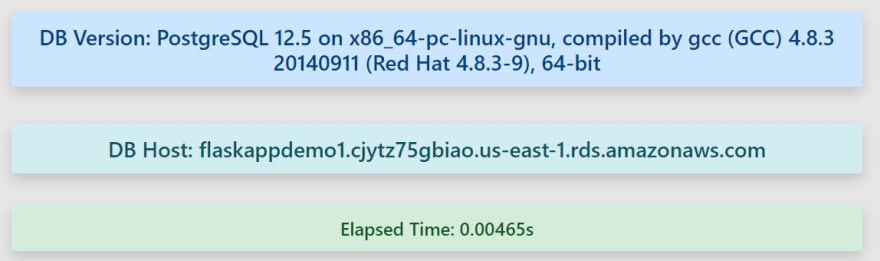


As you can see our next 3 page loads, loaded much faster than our first time when we loaded the page. The cache TTL is configured to last 20sec(for development purposes), after that it will query our database again and save the new results to cache.
Conclusion
I learned a great deal on this challenge and also read a great deal of the AWS whitepapers and resources for research into CloudFormation and ElastiCache especially. These challenges by ACloudGuru has been a great help in challenging myself to build and use AWS. The resume challenge and then this one was fun in helping me prepare for the AWS Developer Associate exam and looking forward to seeing them bring out more AWS challenges going forward.






Top comments (0)