What is ATT&CK ?
MITRE (Massachusetts Institute of Technology Research and Engineering) ATT&CK stands for Adversarial Tactics, Techniques, & Common Knowledge.
The goal is to develop specific threat models and methodologies by bringing communities together to solve problems for a safer world.
In this blog, I will explain all the techniques and tactics matrix in a easier way. This blog is written as a crux of MITRE ATT&CK.
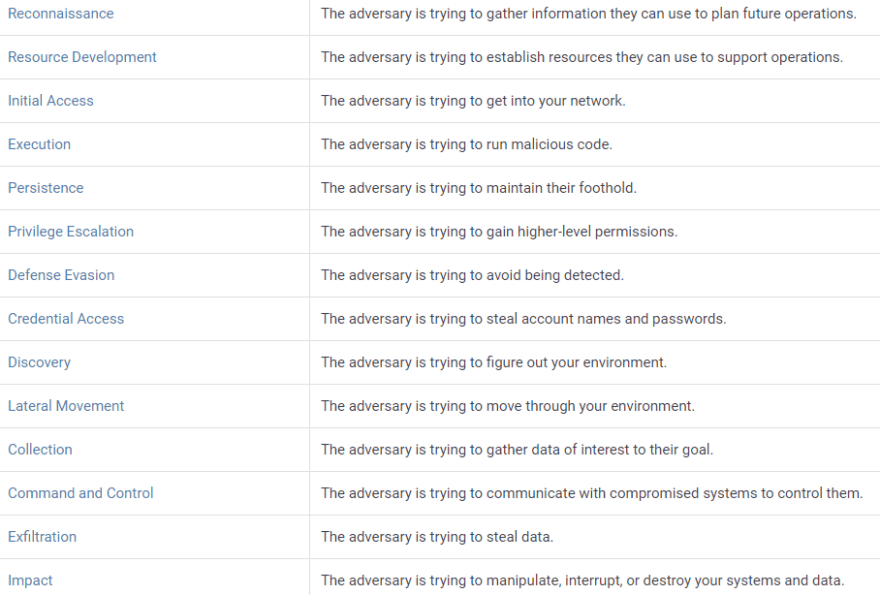
ATT&CK has 14 Techniques that make up an attack chain:
1. Reconnaissance :
Attackers try to collect information of the victim organization, infrastructure, or staff/personnel in order to plan and execute Initial Access and other tactics.
Before compromising a victim, attackers perform :
- Active scan the victim infrastructure via network traffic.
- Attackers collect every hardware and software detail, configuration, architecture, network information, Personal data, credentials, etc..
2. Resource Development :
After gathering details, Attackers try to establish resources they can use to support and perform attack/operations or exploit it.
Before compromising a victim, attackers perform :
- Acquire required infrastructure that can be used during targeting in order to exploit vulnerabilities.
- Compromise the victim's social media accounts.
- Build a malware and automation stuff to perform exploitation.
3. Initial Access :
After establishing resources, Attackers try to get into the network exploiting those security weakness and gain initial access.
Before compromising a victim, attackers use techniques and gain a foothold includes these attacks.
- Malware Attacks
- Phishing Attacks
- Man in the Middle Attack
- Dos/DDos Attacks
- SQL Injection
- Cross-site Scripting
- Business email compromise
4. Execution :
After having initial access into systems, Attackers try to execute malicious code and compromises system/network and also emerge a backdoor in order to have repeated access into system.
Before compromising a victim, attackers perform :
- Run command and script interpreters to execute commands, scripts, or binaries to compromise.
- Disturb the regular functioning of Scheduled Task/Job
- Abuse System services like changing admin controls, run malicious codes, etc...
5. Persistence :
After compromising the victim's system, Attackers try to maintain their foothold in the victim's network. This is the toughest job for the attackers to stay in the victim's network.
Before compromising a victim, attackers perform :
- Keep access to systems across restarts, changed credentials, and other interruptions that could cut off their access
- Account Manipulation, Create an Account, Create or Modify System Process, Perform some [attacks.](https://dev.to/varaprasad_gudi/common-cyber-attacks-i9n)
6. Privilege Escalation :
After successful Persistence in the victim's network, Attackers then try to gain higher-level permissions by exploring a network with unprivileged access.
Before compromising a victim, attackers perform :
- Abuse System services like changing admin controls, run malicious codes, etc... and bypass User Access Controls.
- Hijacking Execution Flow, Abuse credentials of existing accounts as a means of gaining Initial Access, Persistence, Privilege Escalation, or Defense Evasion.
7. Defense Evasion :
After having access to higher-level permissions, Attackers try to avoid being detected by uninstalling/disabling security software or obfuscating/encrypting data and scripts. This is the important step for the attackers to stay stable and active in the victim's network.
Before compromising a victim, attackers perform :
- Take advantage of built-in control mechanisms in order to escalate privileges on a network and Modify Authentication Process.
- Exploit a system or application vulnerability to bypass security features. Hide artifacts, users, files, etc..
8. Credential Access :
After surviving themselves in the network, Attackers now try to steal the credentials like account names and passwords . This is the actual reason/step for their entry into the victim's network.
Before compromising a victim, attackers perform :
- Brute force attack, extract credentials from saved data, Forced Authentication, keylogging, Man-in-the-Middle attack, Modify Authentication Process, Network Sniffing, etc..
- They also perform some famous [cyber attacks.](https://dev.to/varaprasad_gudi/common-cyber-attacks-i9n)
9. Discovery :
After successful hack of credentials, now attackers will be trying to figure out victim's system and internal network. This is the similar step like reconnaissance but it is examined inside the victim's network after initial access.
Before compromising a victim, attackers perform :
- Get a listing of accounts on a system or within an environment.
- Active scan the victim infrastructure via network traffic.
- Attackers collect every hardware and software detail, configuration, architecture, network information, Personal data, credentials, etc..
10. Lateral Movement :
Lateral Movement consists of techniques that adversaries use to enter and control remote systems on a network.
Before compromising a victim, attackers perform :
- Remote access in the network/system.
- Emerge a backdoor in order to have repeated access into system.
11. Collection :
After successful hack of credentials, now attackers will try to gather information and the sources information is collected from that are relevant for the attacker's plan of objectives. The next goal after collecting data is to steal (exfiltrate) the data.
Before compromising a victim, attackers perform :
- Archive Collected Data
- Audio Capture, Video Capture, keylogging, Relevant Data from Local System, Email Collection, etc..
12. Command and Control :
After the attacker collects all the required data, now attacker tries to communicate with compromised systems to control them.
Before compromising a victim, attackers perform :
- Using application layer protocols to avoid detection/network filtering by merging in with existing network traffic.
- Communication Through Removable Media.
- Use a connection proxy to direct network traffic between systems or act as an intermediary for network communications to a command and control server to avoid direct connections to their infrastructure.
13. Exfiltration :
The next goal after collecting data is to steal (exfiltrate) the data.
Before compromising a victim, attackers perform :
- Steal data using network attacks like weak authorization, weak DOS, weak intrusion detection systems.
- Exploring via software attack surface, perform physical attacks like using hardware devices.
- Digital attack surface that is accessed from remote access location.
- Social Engineering / Human attack surface.
14. Impact :
This is the last step for the attacker. After performing all these stages, now attacker tries to manipulate, interrupt, or destroy your systems and data.
Before compromising a victim, attackers perform :
- Account Access Removal/deletion.
- Data Manipulation/deletion.
- Disk Wipe, System Shutdown/Reboot.
IN SHORTS :
There are a number of ways an organization can use MITRE ATT&CK matrix and get benefited.
-- Written by Gudi Varaprasad















Top comments (0)