Azure Policy
Planning out a consistent cloud infrastructure starts with setting up policy. Your policies will enforce your rules for created resources, so your infrastructure stays compliant with your corporate standards, cost requirements, and any service-level agreements (SLAs) you have with your customers.
Azure Policy is an Azure service you use to create, assign and, manage policies. These policies enforce different rules and effects over your resources so that those resources stay compliant with your corporate standards and service level agreements.
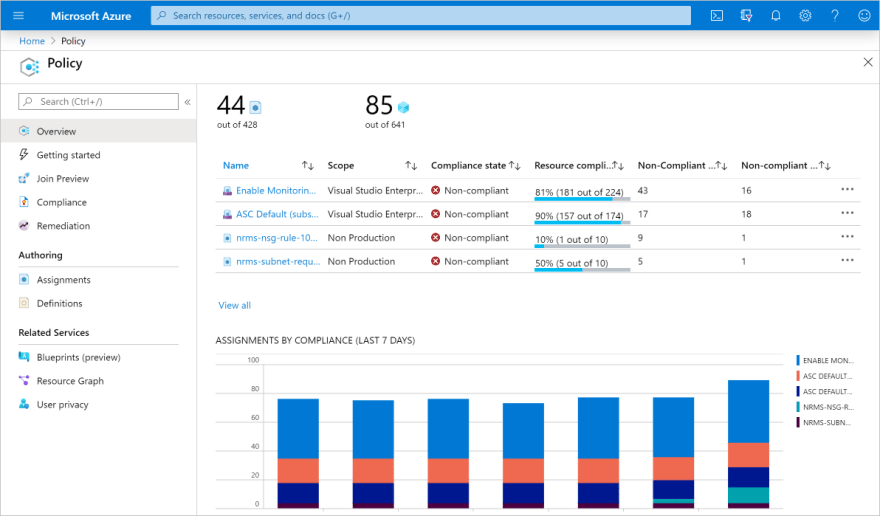
To apply a policy, you will:
- Create a policy definition:
- Assign a definition to a scope of resources
- View policy evaluation results
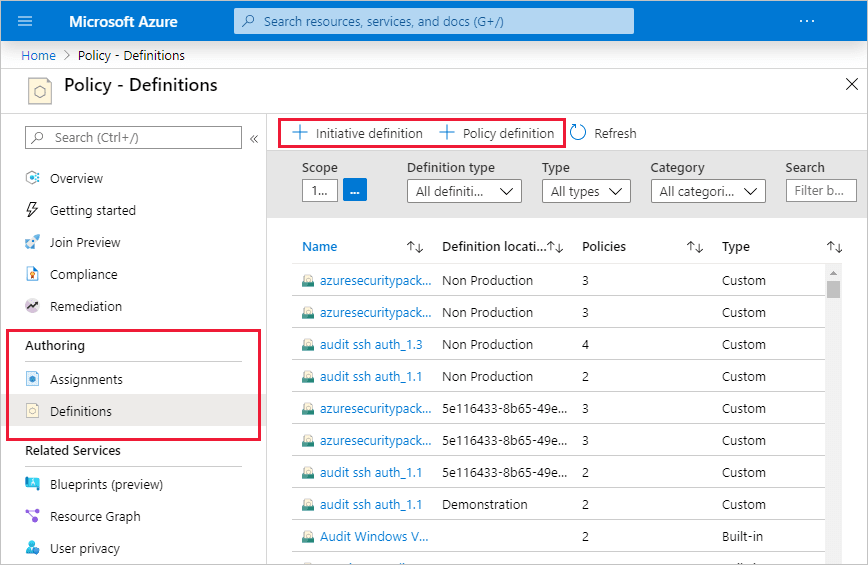
Policy Definition
- A policy definition expresses what to evaluate and what action to take.
- common policy definition can apply to Allowed Storage Account SKUs, Allowed Resource Type, Allowed Locations, Allowed Virtual Machine SKUs
- The policy definition itself is represented as a JSON file.
- To apply a policy, we can use the Azure portal, or one of the command-line tools such as Azure PowerShell by adding the Microsoft.PolicyInsights extension.
- Once we have registered the provider, we can create a policy assignment.
- A policy assignment is a policy definition that has been assigned to take place within a specific scope.
- We can use the applied policy definition to identify resources that aren't compliant with the policy assignment through the Azure portal
- Azure Policy can allow a resource to be created even if it doesn't pass validation. In these cases, you can have it trigger an audit event that can be viewed in the Azure Policy portal, or through command-line tools.
- Finally, you can delete policy requirements through the portal, or through the PowerShell command Remove-AzPolicyAssignment as shown below.
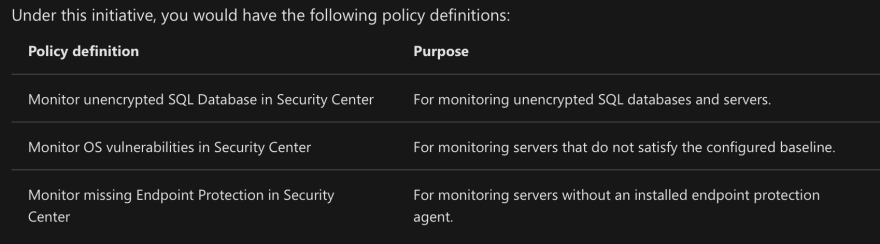
Organize policy with initiatives
- Managing a few policy definitions is easy, but once you have more than a few, you will want to organize them. That's where initiatives come in.
- An initiative definition is a set or group of policy definitions to help track your compliance state for a larger goal.
- an initiative assignment is an initiative definition assigned to a specific scope. Initiative assignments reduce the need to make several initiative definitions for each scope.
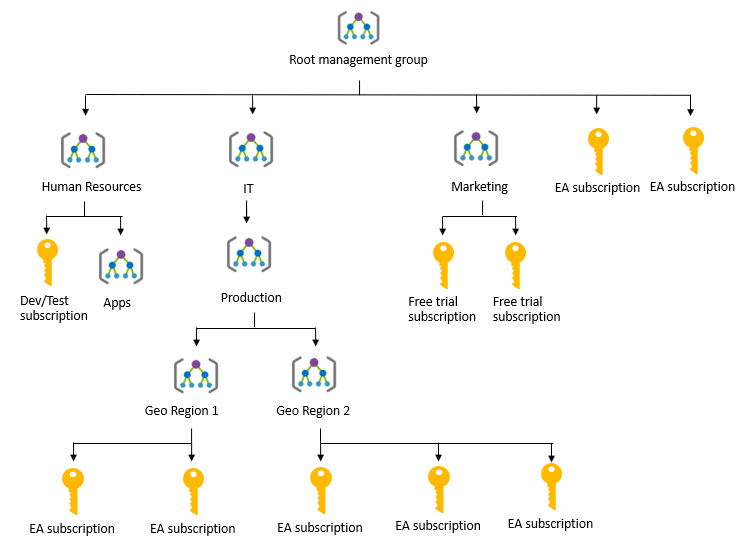
Manage access, policies, and compliance across multiple Azure subscriptions
- Azure Management Groups are containers for managing access, policies, and compliance across multiple Azure subscriptions.
- Management groups allow you to order your Azure resources hierarchically into collections, which provide a further level of classification that is above the level of subscriptions.
- You can manage your Azure subscriptions more effectively by using Azure Policy and Azure role-based access controls (RBACs).
Root Management Group
Create your first management group by entering a management group ID and display name.
A root management group is created in the Azure Active Directory (Azure AD) organization. By default, the root management group's display name is Tenant root group. The ID is the Azure AD ID.
After this group is created, all existing subscriptions in the Azure AD organization are made children of the root management group.
Create additional management groups by selecting Add management group.
Important facts about management groups
- Any Azure AD user in the organization can create a management group. The creator is given an Owner role assignment.
- A single Azure AD organization can support 10,000 management groups.
- A management group tree can support up to six levels of depth not including the Root level or subscription level.
- Each management group can have many children.
- When your organization creates subscriptions, they are automatically added to the root management group.
Azure Blueprints
For auditing, traceability, and compliance of your deployments, use Azure Blueprint artifacts and tools.
Just as a blueprint allows an engineer or an architect to sketch a project's design parameters, Azure Blueprints enables cloud architects and central information technology groups to define a repeatable set of Azure resources that implements and adheres to an organization's standards, patterns, and requirements.
Azure Blueprints is a declarative way to orchestrate the deployment of various resource templates and other artifacts, such as:
- Role assignments
- Policy assignments
- Azure Resource Manager templates
- Resource groups
The process of implementing Azure Blueprint consists of the following high-level steps:
- Create an Azure Blueprint
- Assign the blueprint
- Track the blueprint assignments
With Azure Blueprint, the relationship between the blueprint definition (what should be deployed) and the blueprint assignment (what was deployed) is preserved. This connection supports improved deployment tracking and auditing.
The Azure Blueprints service is designed to help with environment setup. This setup often consists of a set of resource groups, policies, role assignments, and Resource Manager template deployments. A blueprint is a package to bring each of these artifact types together and allow you to compose and version that package—including through a CI/CD pipeline. Ultimately, each setup is assigned to a subscription in a single operation that can be audited and tracked.
Resource Manager template is a document that doesn't exist natively in Azure. Resource Manager templates are stored either locally or in source control.
Compliance Manager
You also have to understand how the provider manages the underlying resources you are building on.
Microsoft takes this management seriously and provides full transparency with four sources:
- Microsoft Privacy Statement
- Microsoft Trust Center
- Service Trust Portal
- Compliance Manager
Microsoft Privacy Statement
The Microsoft privacy statement explains what personal data Microsoft processes, how Microsoft processes it, and for what purposes.
Microsoft Trust Center
Trust Center is a website resource containing information and details about how Microsoft implements and supports security, privacy, compliance, and transparency in all Microsoft cloud products and services.
It Provides:
- In-depth information about security, privacy, compliance offerings, policies, features, and practices across Microsoft cloud products.
- Recommended resources
- Information specific to key organizational roles, including business managers, tenant admins or data security teams, risk assessment and privacy officers, and legal compliance teams.
- Cross-company document search
- Direct guidance and support
Service Trust Portal
The Service Trust Portal (STP) hosts the Compliance Manager service, and is the Microsoft public site for publishing audit reports and other compliance-related information relevant to Microsoft's cloud services.
STP also includes information about how Microsoft online services can help your organization maintain and track compliance with standards, laws, and regulations, such as:
- ISO
- SOC
- NIST
- FedRAMP
- GDPR
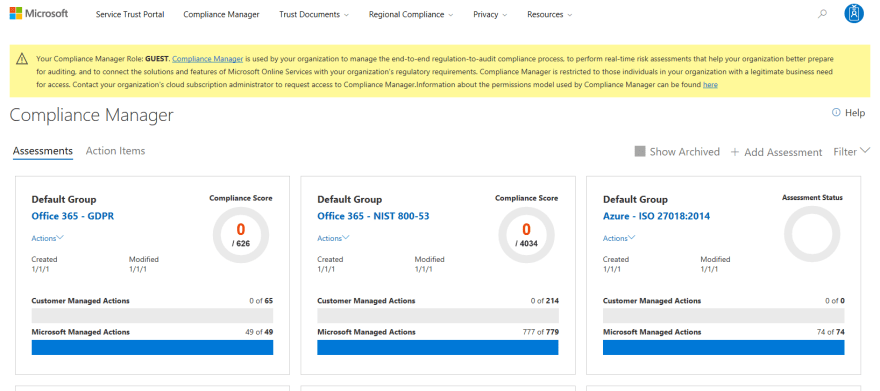
Compliance Manager
Compliance Manager is a workflow-based risk assessment dashboard within the Service Trust Portal that enables you to track, assign, and verify your organization's regulatory compliance activities related to Microsoft professional services and Microsoft cloud services such as Office 365, Dynamics 365, and Azure.
Compliance Manager provides the following features:
Combines the following three items:
- Detailed information provided by Microsoft to auditors and regulators, as part of various third-party audits of Microsoft 's cloud services against various standards (for example, ISO 27001, ISO 27018, and NIST).
- Information that Microsoft compiles internally for its compliance with regulations (such as HIPAA and the EU GDPR).
- An organization's self-assessment of their own compliance with these standards and regulations.
- Enables you to assign, track, and record compliance and assessment-related activities, which can help your organization cross team barriers to achieve your organization's compliance goals.
- Provides a Compliance Score to help you track your progress and prioritize auditing controls that will help reduce your organization's exposure to risk.
- Provides a secure repository in which to upload and manage evidence and other artifacts related to compliance activities.
- Produces richly detailed reports in Microsoft Excel that document the compliance activities performed by Microsoft and your organization, which can be provided to auditors, regulators, and other compliance stakeholders.
Azure Monitor
Azure Monitor maximizes the availability and performance of your applications by delivering a comprehensive solution for collecting, analyzing, and acting on telemetry from your cloud and on-premises environments.
Azure Monitor can collect data from a variety of sources.
- Application monitoring data
- Guest OS monitoring data
- Azure resource monitoring data
- Azure subscription monitoring data
- Azure tenant monitoring data
As soon as you create an Azure subscription and start adding resources such as virtual machines and web apps, Azure Monitor starts collecting data.
Activity Logs record when resources are created or modified and
Metrics tell you how the resource is performing and the resources that it's consuming.
Data monitoring:
- Application Insights
- Azure Monitor for containers
- Azure Monitor for VMs
Alerts. Azure Monitor proactively notifies you of critical conditions using alerts
Autoscale. Azure Monitor uses Autoscale to ensure that you have the right amount of resources running to manage the load on your application effectively. Autoscale enables you to create rules that use metrics collected by Azure Monitor.
Visualizations, such as charts and tables, are effective tools for summarizing monitoring data and for presenting data to different audiences.
Azure Service Health
provide personalized guidance and support when issues with Azure services affect you.
It can notify you, help you understand the impact of issues, and keep you updated as the issue is resolved.
- Azure Status provides a global view of the health state of Azure services.
- Service Health provides you with a customizable dashboard that tracks the state of your Azure services
- Resource Health helps you diagnose and obtain support when an Azure service issue affects your resources.



Top comments (0)