How many times have we heard:
“Our employees know about cibersecurity” 😎
or better yet…
“We are a small company, they will not hack us” 🤓
Tell me HOW MANY TIMES??
The other question I ask myself is:
Why do many companies go bankrupt after a cyber attack? Wasn’t it that they had “everything under control”? 🤔
These are one of the few lies that companies tell about cybersecurity. These lies are great for self-delusion and great for cybercriminals.
Cyber attacks are nothing new and with the arrival of the pandemic they have increased a lot. The reason for this is simple: Businesses have gone the digitization path with outdated security measures.
Another reason is that although it has been more than a year and a half since the beginning of the pandemic, many employees prefer to continue telecommuting while the company continues to invest the same OR LESS in its cybersecurity plan despite being an easier target for an attacker.
The severity is so great that according to data from Sophos, one of the world’s leading cybersecurity companies and collected by the startup NUUBB, specialized in cloud services for companies, shows the top 10 reasons why companies do not invest in cybersecurity.
We are a small company, I don’t think we are the target of a Hacker🤓
This is the first lie that companies tell to deceive themselves. Most of the organizations that have been victims of cyberattacks are precisely because they believe that they are not “attractive” to an attacker. The reality is that ANY company (both large and small) with which it has a minimum of digital presence, is already a good target for a cybercriminal.
Another reason is that most small business cyberattacks are not carried out by professional hackers, but by “opportunists” looking for easy prey, such as small companies that have a low cybersecurity investment believing that they are not attractive to a cybercriminal.
We don’t need advanced security technologies installed everywhere 🤓
Many IT teams still believe that security software is more than enough to stop attacks and they don’t need security for their servers. The reality is that the list of attack techniques that try to avoid detection by IT security teams is growing. Some of the clearest examples are social engineering, memory injected malware, compressed malicious code or “fileless” malware attacks.
Another bad habit is to leave the servers unprotected. The reality of this is that servers are the main target of cyber attackers, since it would simply be enough for them to steal access credentials with social engineering. And this doesn’t just apply to Windows, in fact, cybercriminals often install backdoors on Linux machines to use as safe havens and maintain access to a target’s network.
For all these reasons, cloud experts continue to insist that, even having security policies, an antivirus, a firewall and a 24/7 operations center … the probability that a cyber attacker will find a way to hack the system, is high.
We have very good security policies🤓
Clearly a company must have security and user policies. But they must be reviewed and updated every time changes are made or new devices connected to the network are added. The best way to verify these policies, experts say, is to test them using control sessions, pentesting tests, and tests of disaster recovery plans.
Servers can be protected by changing the service ports and with double authentication 🤓
Yes, we know that the RDP default port is 3389, that the SSH port is 22 and that the SMB port is 445. At first glance, changing that default port seems like a VERY good way to prevent attackers from finding open ports, But reality is not like that.
Computer or network scans will identify any open services, regardless of port. Let’s see an example 👇
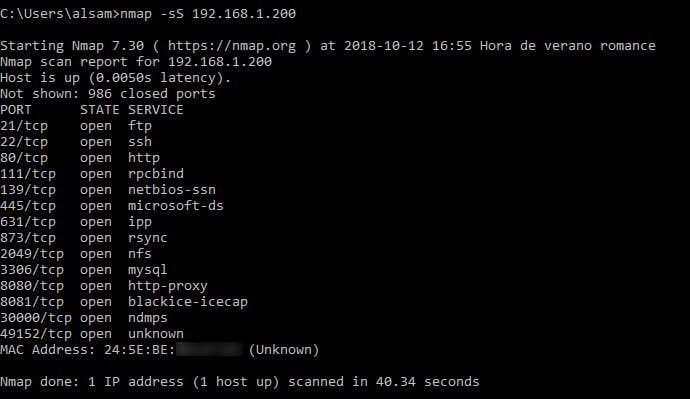
We are going to use the nmap tool to scan a computer on our network to see what it returns.
nmap -sS 192.168.1.200
We can see that in 40 seconds, nmap has scanned the entire range of ports, returning only the open ones.
This change the default ports, it is only a waste of time since the level of protection it offers is null.
We block IPs from Russia, China and North Korea that seem dangerous 🤓
Have you heard of Proxy or VPN? Their main function is to avoid the direct connection of the user with the server, that is, they allow to hide the user’s IP so that the server to which they are connecting cannot know it.
This would allow an attacker from Russia (for example) to connect to a VPN by obtaining an IP address from another country, so blocking would no longer do any good.
Besides, blocking IPs from some countries is unlikely to cause any harm, but it could give a false sense of security. Cybercriminals can be found anywhere in the world, with access points that include the US, the Netherlands, and the rest of Europe.
We have updated backups in case of Ransomware 🤓
It is clear that backups are very important for the company and above all update them on a daily basis. The problem comes when in most companies, those backup copies are connected to the network. With that they are vulnerable to any Ransomware that can erase or encrypt them. In this case, from ByteHide we always recommend following the 3:2:1 SYSTEM 👇
3 copies of everything
Using 2 different systems
Of which 1 is always disconnected from the network
Our workers know about security🤓
According to the State of Ransomware 2021, 22% of organizations believe they will be affected by ransomware in the next 12 months because it is difficult to prevent end users from compromising security.
The easiest techniques are phishing emails and social engineering. Many times these messages are handwritten and addressed to the right person.
Will a worker really know how to detect that message among the thousands that can reach him per month? 🤔
We have recovery systems in case of Ransomware 🤓
Attackers today make far fewer mistakes and the encryption process has improved, so relying on experts to find a loophole that can undo the damage is extremely rare. Automatic backups such as Windows Volume Shadow Copies are also removed by most modern ransomware and overwrite the original data stored on the disk, making recovery impossible beyond ransom payment.
We can pay the ransom of a Ransomware 🤓
Other data emerging from the 2021 ransomware state, a ransom-paying organization recovers on average around 65% of its data. A meager 8% recovered all their data and 29% recovered less than half. Therefore, paying the ransom, even when it seems like the easiest option and is covered by the cyber insurance policy, is not an easy solution to recover. Similarly, restoring data is only part of the recovery process. In most cases, ransomware completely disables computers, and software and systems must be rebuilt from scratch before data can be restored.
If we survive a Ransomware we will be fine 🤓
Ransomware is just the point where criminals want the company to know that they are there and what they have done. Adversaries have likely been on a network for days, before launching ransomware, exploring, disabling or deleting backups, finding machines with high-value data or applications to target for encryption, deleting information, and installing payloads. additional tools such as rear doors. Maintaining a presence on the victim’s networks allows attackers to launch a second attack if they choose.
In the words of Nicolas Blasyk, CEO of NUUBB, “it is very important to be clear that we live with cybercriminals, becoming more present and stronger after the pandemic, taking advantage of those security gaps that SMEs have suffered due to the forced acceleration of digitization. At NuuBB We believe it is essential to raise the awareness of employees about the types of attacks they may suffer, since some of them we can avoid ourselves, such as phishing, malicious emails that most of the time we do not realize, we click on the link and we fall into the trap. One of the best solutions to prevent these attacks that we always recommend is the outsourced Backup service with data recovery “.






Top comments (0)