what is SIEM:
Security information and event management provide real-time analysis of security alerts generated by applications and network equipment.
In this blog we will use the term SIEM and Threat Hunting Tools interchangeably.
SIEM tools basically only provide hints or indicators that there might be a threat on the system or somewhere on the network. Then after that, some people like security analysts have to monitor the processes, mitigate this threat and document the case as part of the business process.
Therefore, it is important to note that the human brain is required to analyze and track a security case, since a SIEM tool cannot be implemented without a security control center or the SOC. It can be one person, it can be 20 people or more, depending on the requirements and size of the corporate network.
In other words, a company cannot implement SIEM and expect the tool to do all the security work for them.
This may lead to the question, what is a SOC?
Abbreviated as SOC (Security Operations Center), SOC is a collaborative work of security analysts, team tools, and processes to achieve the common goal of monitoring, discovering, and investigating the entire network and endpoints of a company in order to reduce the attack surface by detecting potential risks and threats. and proactively respond to them before they reach their endpoint or company network goals.
Why do we need a SOC (Security Operations Center)?
This is more of a business question than a technical one. Never try to justify an SOC claim in terms of the technical benefits it brings when we offer a business-required solution. The cost of an SOC should be justified to senior executives and management in terms of its impact on the business, not the technical performance and wonders it can create.
The most typical reason is the compliance auditing, which periodically happens for many respective companies that mostly external auditors are contracted to check and audit the overall security aspects of the company. If the compliance auditing produces negative results, it directly affects negatively the contracts that the company holds with its customers, and as a result, customers lose trust. So, in the end it will be a loss for the company.
Another reason is that the company decided to voluntarily increase its security awareness by monitoring the integrity of its security measurements to avoid threats and attacks surface across on the company's network.
Having said that, this leads to the question of what should be monitored by the SOC (Security Operations Center).
Again, this question cannot be answered at a technical round table.
From management to other relevant stakeholders, the company should also be involved in the decision-making process to determine which business processes, which applications, which critical endpoints, and which data should be monitored. where the log files will be stored and for how long. Who will have access to these log files and questions are sought after these sorts of business decisions have been made.
It is time to talk to techies like the IT department and check what kind of log data are being already collected from security applications or appliances in the company, and then check what lightweight data is missing for SOC purposes. So, cover them with SIEM as well.
Despite covering only critical and important log sources, the log data will slot from different sources like Firewalls, Ids, End points, Active Directory is probably some important IOT’s and so on, so it's going to be huge. Therefore, it will call for pre decisions to be made. How to handle that data lake.
For now, it is important to note that there are three points required to be well planned to run a successful thread hunting tool.
1) First Lots of Log Data.
In other words, no lots of logs, no working threat hunting tool
2) Second, Well Trained Security Analysts.
These are people who are trained as a security analyst and are familiar with the environment of the company and the context of those log files that are being generated every day. This is very crucial.
3) Third, Cyber Threat Intelligence
Threat intelligence is data that is collected processed and analyzed to understand a threat, actors, motives, targets and attack behaviors.
All these points are required for a threat hunting tool to be a useful and functional and purposeful feeling, all these three points are required for a threat hunting tool to be successful, but do not rely on threat hunting tool to do your job because well-trained analysts are needed. So, for this lecture/blog whatever you call it, it is important to understand that SIEM is just a tool and SOC is consisted of SIEM and other tools, plus analysts, people and procedures to detect, hunt and respond to the unknown.
How SIEM Works
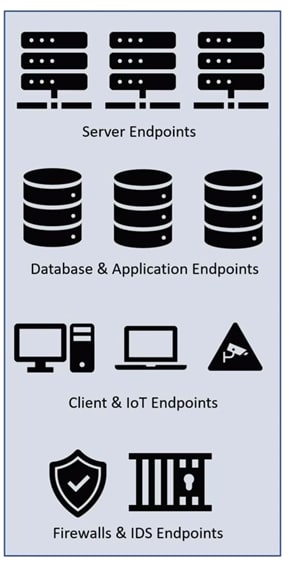
This is how a company's network looks like in terms of assets.
They have different servers, storage storages. We should process or store large amount of data.
Then we have endpoints or clients such as Windows or Linux clients, along with IOT like cameras and so on, operational or industrial computers, all that constitute a company's assets. All of them are connected via switches and routers. And finally, there are some security apparatus such as firewalls and IPS IDS, which stands for intrusion prevention system and intrusion detection system, which observe the traffic and decide what can go through the company's network and what is not allowed.
This leads to the question.
There are already security tools there where the SIEM sits in the company's network SIEM tool is not a preventive security tool like firewall, anti-malware or IPS.
What it does is collecting every possible log data from different sources that we connect them to the SIEM system from servers and network devices to applications and databases, and it is towards them in a database. Great portion of the data collected from firewalls, IDS, network devices and so on are in this Syslog because almost all these appliances can speak Syslog, which is a standard protocol for message logging, for operating systems and point and servers such as Active Directory or Linux servers.
We can install an agent which normally comes with the SIEM tool company itself or its community, the same agent, and will collect and send the relevant security log data to the central log server of the SIEM.
As I mentioned, all these events and logs are coming in different log format. One of the same log manager duties is to consolidate and unify these logs, so-called log normalization and install them all unified in a same database.
The reason for this normalization is that later search and log analysis through the huge SIEM database will be much more reliable, performance optimized and quick to process, when log data are collected, normalized and analyzed, there are two possibilities creating a dashboard, using a small widget that many of the SIEM tools, including ELK stack offer. You will see this dashboard later.
Second possibility is creating rule rules or rule-set or a small pieces of query code, each of which resembles a pattern for a security use case we are interested in, and when that security use case happens anywhere in the company's network or any of the endpoints, we will get alarmed. Again, you will see these in action later on in this blog. For now, it is just an introduction. We just keep it theory to build up some fundamentals and then later on you will see them all in action.
After the alarms are triggered. And it is a SOC’s part to investigate the alarms. If they are really an attack incident or a security case or just a false positive.
One outcome of all this process can be Audit Compliance. Many well-structured companies are being audited by auditing companies, most of these auditing companies are external companies who just do auditing, who check if the company comply with the latest security standards or not. If a company does not pass its auditing process, it can have directly a negative effect on its business.
It's as simple as that.
The other outcome is I.T. security. Every company would like to stay safe and sound from cyber-attacks here does SIEM at least can help the security team of the company to have a better view on its network in terms of user behaviors and vulnerabilities, in different systems.
So, in general, this was how SIEM works.
we will discuss SIEM Use Cases and Common Mistakes in the next blog or I will just update this one instead.
Thanks for reading. See in the next blog.





Top comments (1)
That's one eye opening content