Long story short: I had an issue in Windows which prevented me from booting from my NVME SSD drive in my laptop. In order to install a fresh copy of Windows to that drive without losing any data stored on it, I needed to decrypt the drive. It turns out you can't install onto an encrypted disk. To decrypt a disk, you need to be logged on... I ended up using Windows-to-go to solve my problems
Mount the drive in a different system
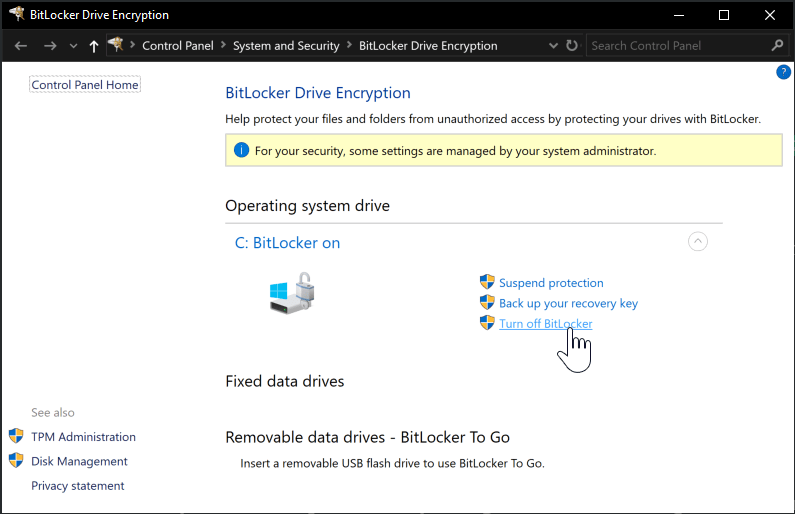
The easiest way to solve this problem is by taking the drive and adding it to another system that already runs Windows, boot into that system, unlock the data partition using the BitLocker recovery key and then decrypt it from the BitLocker control panel:
However, this requires access to a system with a spare NVME slot you can install the drive into. Turns out that most laptops in our company only have a single slot which is already taken by the primary OS disk.
Start Windows in Recovery mode
If there is a local administrator available on the system, you can possibly use that to launch into recovery mode and decrypt BitLocker from there. My system is Azure Active Directory joined and doesn't have a local administrator. That rules out this option as well.
Windows-to-go to the rescue
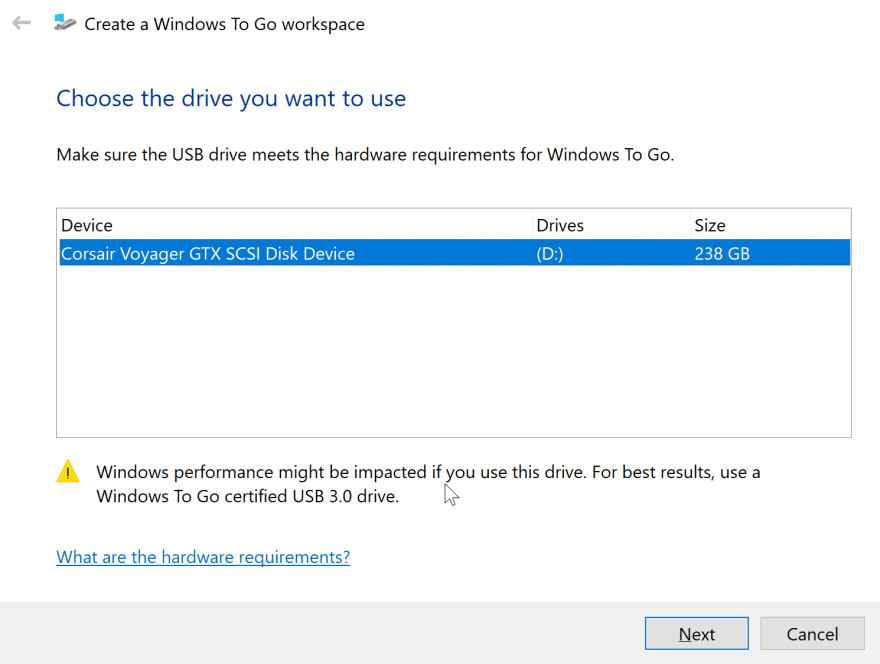
After going through many different options that all turned out to be fruitless, I remembered Windows-to-go. Windows-to-go is basically a way to launch Windows from a USB key. I downloaded Windows 1703 Enterprise Edition (there is a bug in 1809 that will cause a blue-screen) from my visual studio subscription and used Rufus to create a Windows-to-go USB key.
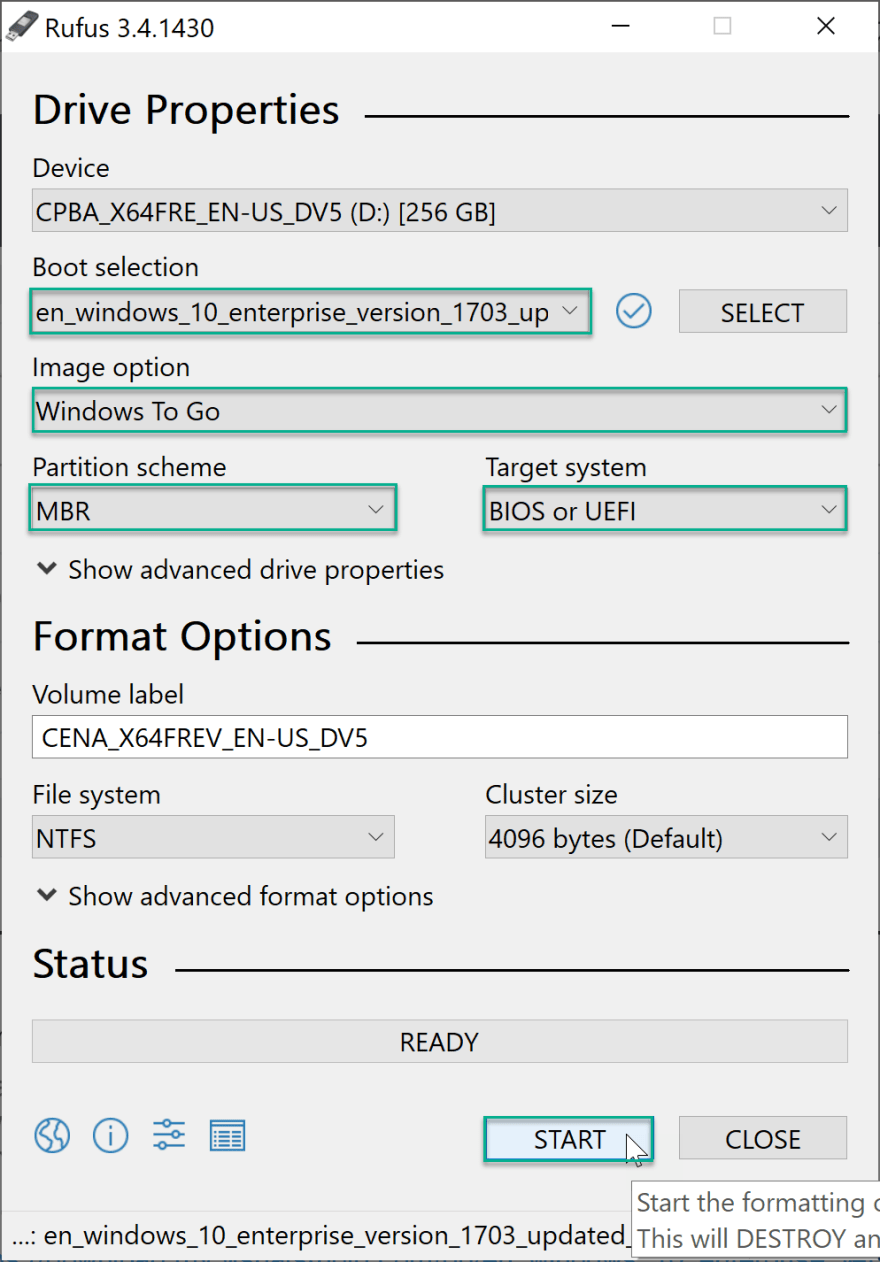
Insert the USB key into the troublesome system, select it as boot device (optionally turn off Secure Boot) and let it reboot a couple of times until you are presented with a Windows Desktop.
Find the affected drive in Windows Explorer (it will show a lock icon on the drive) and enter the BitLocker Recovery Key to unlock the drive. Now you can open the BitLocker Control Panel en decrypt the drive.
Use the Windows Image Download tool to create a setup drive
Now use the Windows Media Creation Tool to build a Windows 10 setup image and install a fresh Windows 10 over the broken one. You'll have to reinstall all your applications after this, but you won't lose any documents when done correctly.
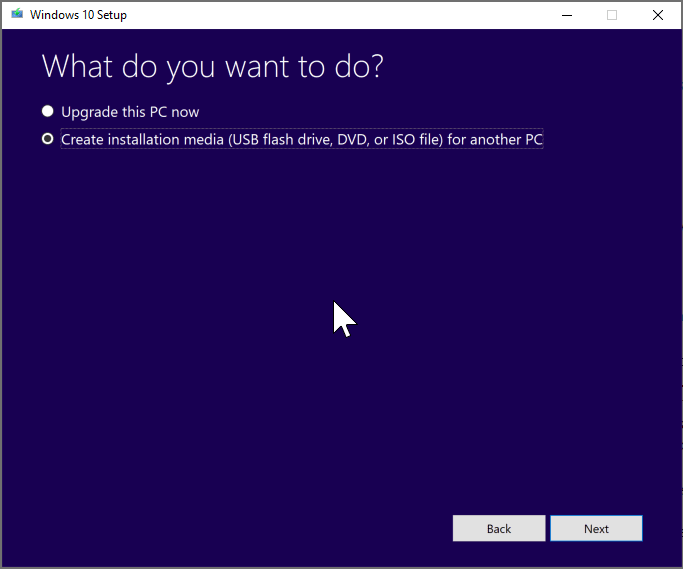
I had used Rufus before to create a bootable Windows Image, but somehow those can't install windows onto a GPT partitioned hard-drive, the USB key provisioned by this tool can.
Lessons learned
So as always when working with BitLocker:
- Make sure you have a backup of your BitLocker Recovery Key. In my case it's uploaded to Azure Active Directory and stored in 1Password.
- Create a local admin account with a very complex password in case of emergency. That way you can boot into a Windows Recovery Console and get your data out.
- Have a Windows-to-go compatible USB key.
I used this one:
While not certified, it worked like a charm:
Yay!
While I have much of my data synced to a cloud storage account, Azure Backup configured, my projects in Azure DevOps or GitHub, it's still much easier to just have all my files where "they are supposed to be" on a drive where I can access them at 300 MB/s.
I'm up and running again.




Top comments (0)