Day-7: I started my day watching Dude perfect's documentary and ended it learning Nmap and about its scan types! Also, In between, I bought pentesterlab pro access (3mths - Student access).
Note: I won't be writing more in deep, but my notes! And will be providing all the links/resources (Don't forget to check-out the resource section) from where I learned so that you can refer to that resource and learn more! Thanks!❤️
What is Nmap?
- Nmap stands for Network Mapped (Nmap) and is a network scanning and host detection tool that is very useful during several steps of penetration testing.
- Nmap is open source and can be used to:
- Detect the live host on the network (host discovery)
- Detect the open ports on the host (port discovery or enumeration)
- Detect the software and the version to the respective port (service discovery)
- Detect the operating system, hardware address, and the software version
- Detect the vulnerability and security holes (Nmap scripts)
Nmap Syntax:
nmap [scan type] [options] [target specification]
Nmap Scan types:
- TCP SCAN
- UDP SCAN
- SYN SCAN
- ACK SCAN
- FIN SCAN
- NULL SCAN
- XMAS SCAN
- RPC SCAN
- IDLE SCAN
Using Nmap help:
- The best way to get used to nmap and its flags is using
nmap -h, run this command in the terminal and will give you the following results: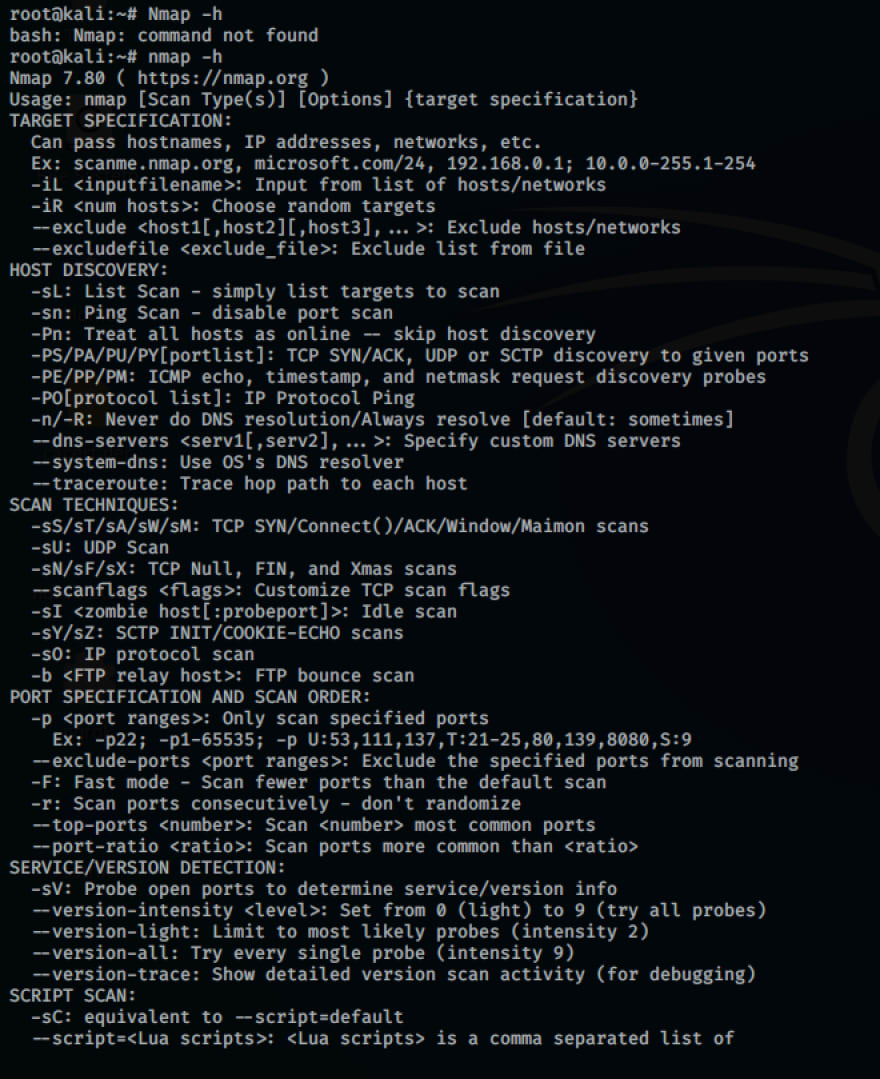 and one more screenshot, but it is creating a mess so wont post it! Try yourself and explore the world of nmap! Happy Scanning!
and one more screenshot, but it is creating a mess so wont post it! Try yourself and explore the world of nmap! Happy Scanning!
Port states recognized by Nmap?
- Six port states recognized by Nmap are:
- Open
- Closed
- Filtered
- Unfiltered
- Openfiltered
- Closedfiltered
Resources:
Medium Blogs: https://medium.com/bugbountywriteup/intro-to-nmap-192c1796bb39
Nmap Installation: https://nmap.org/download.html
HackerSploit Nmap Tutorial: YouTube
Port Scanning basics: https://nmap.org/book/man-port-scanning-basics.html
Scan Types: Edureka
Contact:
Got doubts? Contact me on Twitter.
Feedbacks are welcomed, do comment it down below! :)



Top comments (1)
Hey Zoe,
Thank you for the feedback!❤️