Blackhat 2022, on its 25th anniversary, took place this week in Las Vegas. It’s the most important event for the infosec community and the best place for security vendors to showcase all their innovations and products in this ever-growing ecosystem. This year, attendees come from 111 different countries.
In 2020, Black Hat added the word Cloud to the existing track about Platform Security. Research on Kubernetes, containers, and other cloud technologies had been presented at Black Hat before 2020, but adding Cloud to the track title really highlighted the importance of securing the cloud that many corporations and individuals rely upon every day.
In summary, we have cloud at the core of most of the talks, eBPF is growing in visibility, and attacking and defending the supply chain as a priority. As a threat, we could say ransomware in the cloud and global conflict management, and finally the importance of early detection of burnout.
In this Blackhat 2022 recap, we’ll share our insights about the talks that we believe to be the most interesting.
Blackhat 2022 – KEYNOTES
In this edition, one of the main topics in the keynotes was the control of information, the problem with how fake news is impacting our lives, and the difficulties of checking reliable information. The solution, in some cases, is to intensify controls on information sharing, but this could be used for censorship. Now it’s not just governments and companies that are involved. New players in the field, individuals, are part of it, and like spam detectors, we need something ethical to protect us.
The invasion of Ukraine is another topic mentioned in the first few minutes of Blackhat 2022. Some companies started to participate, and banned relations with Russian projects or affected domain renewal in Russia. So, the end of these conflicts is all but certain, and instead it seems that they are progressively more chaotic with increasing impacts on society.
Chris Krebs, Director of CISA, explained in one of the Blackhat 2022 keynotes the main four reasons for why it is so bad right now and left us with an important lesson: “Life is too short to work for a**holes.”
Technology: More software means more complexity and, by default, more insecure code integration to maintain and update. In addition, Krebs emphasized how the lack of vision within the cloud causes complex risk management.
Bad actors: Attackers know all this and know the profit is in the cloud. As we mentioned in the anatomy of cloud attacks, cloud ransomware is the future threat and is going to have a big impact. Attackers are betting on targeting the supply chain to gain access.
Government: Regulation, economics, and innovation are growing, but it is very difficult to work with governments efficiently. Compliance must change to get more results than a checklist. We must watch out for future global incidents to be prepared.
People: How do we balance all this information? In most cases, people are the end users of all this technology and the victims of breaches and incidents.
Kim Zetter, investigative journalist, gave a good overview of the evolution of threats and how this impacts companies. The media has had to adapt when it comes to explaining new vulnerabilities or threats to the audience. She mentioned the Pre-Stuxnet and Post-Stuxnet eras, where everything has changed but the same actors remain. She started with ransomware, evolving into more sophisticated malware that modified code to eventually directly affect the supply chain with SolarWinds.
In a real case, she explained that a company with a perfect backup system and everything prepared to be restored (in case it was affected by ransomware) paid the ransom when it happened. Why? It never tested the recovery process. Therefore, we should anticipate and perform simulations just like we do fire drills.
Finally, we all know the good security practices, such as isolating networks, reinforcing perimeters, mfa, IR plan and backups, that protect us from most attacks. But, critical infrastructure is still not fully implemented, remaining exposed and without authentication on the internet.
Blackhat 2022 – Top Briefings
During two days of Blackhat 2022 USA trending sessions, we were able to enjoy several high-level talks on cybersecurity. These are, in our opinion, the most remarkable ones.
IAM The One Who Knocks
One of the most important parts of securing your cloud account is how to manage identity access. In this talk, Igal and Noam provide a good explanation of how each public cloud (AWS, GCP, and Azure) implements access and authorization. Every cloud provider works differently but there isn’t one that is clearly better than the others; the major difference is the scope of the permission. AWS scope is part of the policy itself, and they recommend AWS SSO.
Another important topic was the non-human identities. Each provider calls them something different, but the attackers don’t care. They only like to exploit the Cloud IAM weaknesses and the speakers explain how with different examples.
Here are the takeaways.
Default is the best friend of attackers: Maintaining a good CSPM is crucial to stop the majority of attacker’s attempts to control all your accounts. Avoid temporary fixes that become permanent.
Monitor and protect credentials: Not only is the creation part relevant, but the modification of a compromised account is a huge threat.
Log everything but know the limits: the golden rule of security is to log everything, but in some cases we exceed the limits. Attackers use this to hide their actions and go unnoticed. At this point, we want to highlight another option. Try to detect at runtime or at the time when these logs occur to avoid the large amount of logs (only one window is sufficient if the initial compromise attack is detected). That is what Falco open source tries to do.
Finally, the speakers shared different open source tools that will help you manage excessive permissions. Two types of tools, the constructive (adding only the requirements, the principle of least privilege) and the reductive (default permission and remove from it).
| Constructive | Reductive |
| policy-sentry | Cloudtracker |
| iamlive | Repokid |
| access-undenied-aws | IamSpy |
| PMapper | |
| Cloudsplaining |
Trying to Be Everything to Everyone: Let’s Talk About Burnout
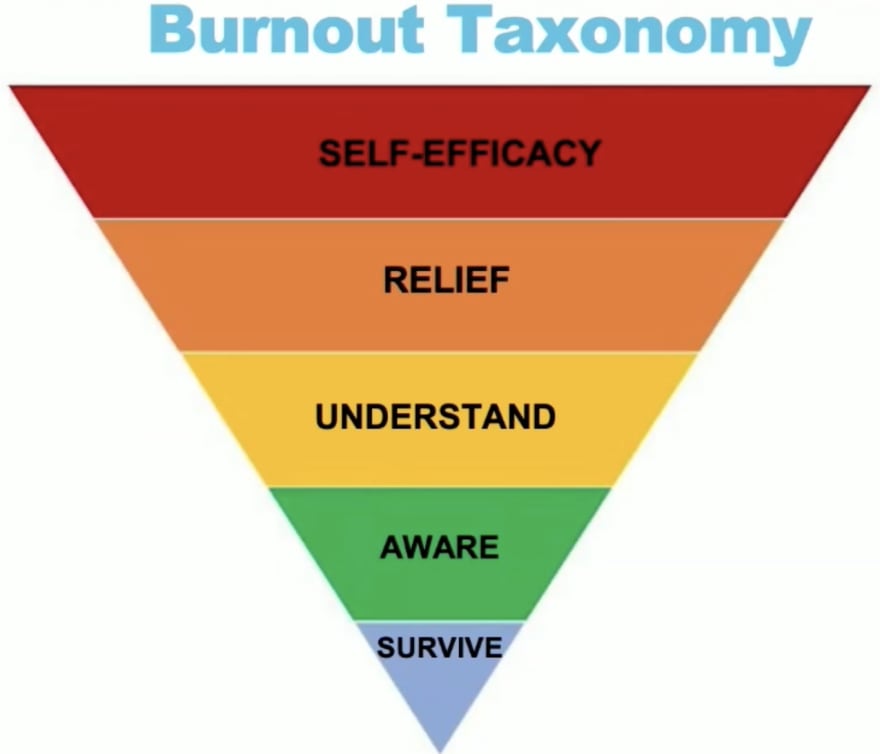
Burnout is no joke. You have to take care of yourself and detect burnout before it is too late. This talk exposed the problems within the security industry, including the high levels of mental workload, the rapid response that security engineers are forced to have when a shortage occurs, and when they must anticipate cyber attacks that lead to maintaining a high level of stress.
Of course, it’s very difficult to quantify security, so it’s hard to know if we’re investing our time and effort (and money!) well. For this reason, we can often feel that we are not doing our job well no matter how hard we try.
The speaker suggests good health, physical fitness, and relaxation techniques. The most common solutions for burnout are to work in short time slots, balance it with your personal life or, if you can, stop working and be free. Joking aside, ask for help at the slightest risk of burnout.
RCE-as-a-Service: Lessons Learned from 5 Years of Real-World CI/CD Pipeline Compromise
We have to go back to basics; this is one of the points to keep in mind. The speakers explained different use cases and examples where the CI/CD pipeline was compromised based on issues that are not new. Examples include exposed credentials encoded in YAML or other configuration files, failure to isolate networks, or not following the principle of least privilege. One of the demonstrations focused on cloud-to-premises hopping, an increasingly common threat.
To solve this problem, one of the things mentioned is the signing process, verify everything we are running. We explain in detail these procedures in Kubernetes by using cosign and connaisseur.
Trace Me if You Can: Bypassing Linux Syscall Tracing
System call traces are used to detect different behaviors within linux systems. There are several tools to obtain this data and process it to generate alerts when something strange happens. Like the Kubecon talk (Bypassing Falco), this talk focuses on the Falco tool and the TOCTOU problem solved in the current version.
TOCTOU, or time-to-check to time-to-user, is a software bug caused by a race condition. In this talk, the speaker simulates how the attacker could modify the trace of a syscall in several scenarios. Here, we summarize two of them:
- The first uses delay injection in the communication between the client (or compromised device) and the server (in this scenario, the C2C). The technique is based on delaying the response in the handshake when the communication is initiated. The communication, when the exploit replaces the original IP with a fake one, is hidden from post-forensic analysis. If we check the network traces in Wireshark, we can discover the real IP of the C2C in the first packets.
- The second scenario is the same idea but on the routes we like to modify. The attack is performed to store information inside GKE, avoiding detection by changing the path of the file we are writing.
The demo is performed exploiting using Phantom-attack, presented at DefCon 29. The mitigation was using the new version of Falco (>0.32), and it is also recommended to use other methods to block the system call such as seccomp. This would affect its performance.
Kubernetes Privilege Escalation: Container Escape == Cluster Admin?
This talk explains the same concept presented at the KubeCon EU with the talk Trampoline Pods.
The scenario presented is as follows: inside our Kubernetes cluster we have containers running, but one of these containers is vulnerable and the attacker gains access to execute commands and control the entire node using container escape techniques.
What is the next step to control the entire cluster? Kubelet’s credentials are not enough, and the node permissions are different to be admin. The goal is to get control of a trampoline pod in DaemonSets to perform lateral moves between nodes and obtain control of the whole cluster. There is no clear list of what permissions are required to carry out this type of attack, but depending on which ones are required, one or the other can be performed.
AuthN/AuthZ: Impersonate to escalate roles.
Acquire Tokens: Create new tokens for privilege escalation and, with the service account, enable secret list and use it to authenticate to the api-server.
RCE: You do not need to escalate privileges to run your code, it depends on your configuration. It controls Kubelet.
Steal Pods: Move the pod from one node to another with a powerful services account. Update nodes or delete other pods permission required.
This Trampoline pod affects all major cloud providers with the default behavior and, for this, escaping the container means managing the entire cluster. They shared the tool rbac-policy that was presented in KubeCon EU.
Cautious: A New Exploitation Method! No Pipe but as Nasty as Dirty Pipe
The new exploitation method presented by Zhenpeng Lin is called DirtyCred and is based on swapping Linux Kernel credentials. It’s simple, effective and generic. This allows it to perform container escape and still be an actual threat.
Exploitation is performed on a system vulnerable to CVE-2021-4154 or CVE-2022-2588, and the speaker explained two path attacks.
Attacking task credentials (struct cred): Our un-privileged credentials inside the kernel heap are modified, free, and privileged credentials are put in the same place to impersonate them.
Attacking open file credentials (struct file): Free the file after checks but before writing to memory. Allocate a read-only file object in the freed memory slot.
To do this deterministic and not wait for privileged users to allocate task credentials, the attacker could trigger privileged processes in user space (executables with root SUIDs or daemons running as root). Finally, the attacker needs to stabilize the file exploit by extending userfaultfd or FUSE (pause kernel execution).
It’s a very interesting exploitation method that requires further research.
DNSSEC Downgrade Attacks
DNSSEC is the solution to DNS, based on cryptography signatures and verification of the resolver with a chain of trust. DNSSEC protects us from DNS Poisoning when we have a compromised application. DNSSEC provides data origin authenticity and integrity, but not confidentiality.
The attack is based on making the resolver use the weakest security path and attacking that weakest link in the chain of trust. The final model is that the attacker, without knowing the cryptographic secrets, is able to activate the resolver, intercept it, and modify the records and signatures. The result? Successful impersonation of a real resolver.
Countermeasures against this are to require the stronger DS and to drop SHA-1.
If you are interested in knowing more about DNS and how to configure it in a secure way in the cloud, read the article How to protect DNS in the Cloud.
Scaling the Security Researcher to Eliminate OSS Vulnerabilities Once and For All
The speakers started with a simple concept. When we detect a vulnerability in open source code, how do we fix it? Well, fork the code and PR with changes inside that resolve the vulnerabilities. But what if this insecure code is in thousands of repositories?
The first vulnerability that was fixed is the download or update of dependencies via HTTP, which are vulnerable to MiTM and not recommended at all. But is it a real problem? Well, Sonatype maven core downloads still use HTTP (25%).
To solve this problem, the speaker creates a python bot with CodeQL and scans 100k with a simple regex.
With this, the bot created over 1,400 pull requests with an acceptance rate of 40%. Pretty impressive. But this is just the beginning. How can it do the same with all the security vulnerabilities within the repository code on a massive scale?
Well, openRewrite has been introduced, an automated software refactoring to keep up to date with API changes, fix vulnerabilities, and improve code quality and the Moderne platform to manage the entire process. The talk explained three vulnerabilities (temporary directory hijacking, Partial path traversal, and Zip Slip) and focused on java language.
What’s next?
This has been the most relevant at Blackhat 2022 USA. The main topics are still Kubernetes security, cloud security, and supply chain attacks, but we have a lot of global incident presence.
In a few months, we will have the next Blackhat in Europe. We hope to be here with more great talks and demos.







Top comments (4)
Thank your for sharing !! 👍😎
You are welcome! :)
Nice summary! Thx!
you are welcome! :)