Zero trust architecture is central to an organization’s security posture to mitigate cyberattacks, and the Defense Department recently released its Zero Trust Strategy and Roadmap on its plan to get the DOD to a Zero Trust architecture by 2027.
A zero-trust architecture provides the foundations for micro-segmentation of the IT landscape, access limited with the Least Privilege principle, and all communication to and between the micro-segments being authenticated, audited, and verified3. The underlying philosophy for zero trust is never assume trust, but continuously validate trust, so bad actors don’t get in. Companies, organizations and government agencies need to make sure that even users inside a network can’t do serious damage.
Conent Syndicated from Data Security through Zero Trust and a Ransomware Strategy
Flag Unusual Behavior
Zero trust principles ensure user access is continuously validated and monitored for Authentication and Authorization while constantly Auditing. Commvault leverages security controls such as multi-factor authentication for everyday administrative tasks, privacy locks, and data encryption. User access can be compartmentalized, explicitly denying CommCell level access, while applying roles to micro-segmented groups of resources through multi-tenant configurations. Zero trust controls help limit internal lateral movement to prevent data loss and unauthorized access to data.
Apply Zero Trust Controls
Commvault makes it simple to apply zero trust AAA controls by using the Security Health Assessment Dashboard. The dashboard provides a single pane of glass for identifying controls, highlighting potential risks within the backup environment, and recommending interactive actions to apply controls.
Add Layers of Security
To help strengthen the resilience of your data infrastructure, the NIST Cybersecurity Framework focuses on five primary pillars for a successful and holistic cybersecurity program. Attention to these pillars can help your organization in developing a comprehensive risk management strategy. Commvault has built these security pillars into our data protection software and policies without the incremental management overhead. The Commvault data protection and management platform include five security layers:
-Identify
- Protect
- Monitor
- Respond
- Recover
Our multi-layered security consists of feature sets, guidelines, and best practices to manage cybersecurity risk and ensure data is readily available. We help protect and isolate your data, provide proactive monitoring and alerts, and enable fast restores. Advanced technologies powered by artificial intelligence and machine learning, including honeypots, make it possible to detect and provide alerts on potential attacks as they happen so you can respond quickly. By keeping your backups out of danger and making it possible to restore them within your Service Level Agreements, you can minimize the impact of a ransomware attack so you can get back to business right away (and avoid paying expensive ransoms).
Immutability
Protecting and isolating your backup copies is critical for data integrity and security. Therefore, we have taken an agnostic approach to immutability. With Commvault, you do not need special hardware or cloud storage accounts to lock backup data against ransomware threats. If you happen to have Write-Once, Read Many (WORM)-, object lock- or snapshot-supported hardware (which Commvault fully supports), you can still use Commvault’s built-in locking capabilities to complement and layer on top of existing security controls. Commvault’s ability to support layered defenses for securing data sets against ransomware ensures that your organization benefits from a sound cyber recovery-ready architecture. Here are some elements to include in your immutability architecture:
- Access locks to isolate copy store against ransomware
- Immutability with lifecycle locks to reduce risks, balanced with consumption impact
- Air-gap isolation network and controls
- Configuration governance to protect against intentional or accidental changes
- Concurrent Recovery performance – reduce latency with due importance to speed and cost impact
- Automatic patching to stay current, simplifying management and maintenance of data protection infrastructure
- Alignment with the 3-2-1 data protection philosophy (3 copies of data, 2 different media, 1 vaulted copy)
Learn more about Commvault’s immutable infrastructure architecture here.
Cyber Deception Technology
While delivering business continuity is a critical element of any multi-layered strategy, a strong security posture also includes proactive defense technology that actively surfaces and engages unknown and zero-day threats. Metallic® ThreatWise changes the game in ransomware protection, combining sophisticated early warning and early action with comprehensive data protection. It enables businesses of every size to neutralize silent attacks before they cause harm, detecting and diverting the stealthiest of zero-day attacks, which evade conventional detection technology and circumvent security controls.
A Ransomware Strategy
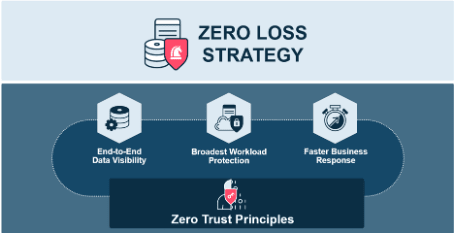
You need a plan to remain steadfast against ransomware. Beyond simply adhering to zero trust principles and hoping for the best, the ultimate solution can manage and substantially reduce the impact of a ransomware attack. It can reduce costs for your organization by utilizing one centralized management platform, so security teams don’t have multiple product points to log in and out of. It can increase the visibility of your data through a single landscape to minimize complexity for your teams. And finally, it can protect what matters most by providing the broadest workload coverage and rapid recovery capabilities through a unified approach. For all of this to happen, a solution must embrace Zero Loss Strategy. Learn more here.
Become Less Vulnerable
The reality is your organization needs to be prepared and take proactive steps to protect your data and work with a provider who offers ransomware protection and recovery solutions. How prepared are you? Take our free risk assessment to find out.






Top comments (0)