When we are talking about authentication and authorization a mix of mess arrive in your head.
The first thing that we have to know is:
- Authentication is a process to know who you are.
- Authorization is the process to know if you can do what you want.
Is easier now? I will show an example.
When you go to access a site and for this is needed inform a login and password, this mean that you need to be authenticated to know who you are.
You access the site and when you try to access some part, as report or admin module, and the site alert you that lack privilege, this process is called authorization. That is, you have authentication but not authorization.
Build an application that take care both authentication and authorization is very hard. But for those who work with ASP.NET Core is recommended to use something called Identity.
Identity is a feature of ASP.NET Core that facilitate the process to create user account, authentication and user privileges (authorization).
Using Identity with Entity Framework get more beautiful, because the Identity will use the Entity Framework's wisdom to access the data base.
But, where the claim starts?
Keep calm, I'm going to explain.
In summary, the claim is an attribute. A person has many claims, below I explain better.
All person has not an attribute but many. A person has a name, weight, height, birth date and many others. This is claim set.
Each claim has an issuer, that is, who issued the claim. When I talk that a person has a weight and height, himself is the issuer. But when I talk about social number of a person, the issuer is the federal government.
Another example. When you make an integration with Facebook and get person data the issuer is Facebook. Do you understand now what is claim and issuer?
What if I use Identity, how use claims?
When the application is using Identity and authenticate a user, as code below, this authentication creates an object of type "ClaimsPrincipal".
For those who do not know Identity, the "SigninManager" class is used to authenticate a user with a name and password. But note, I do not need to access the database to see if the user exists, the Identity with Entity Framework makes this for me.
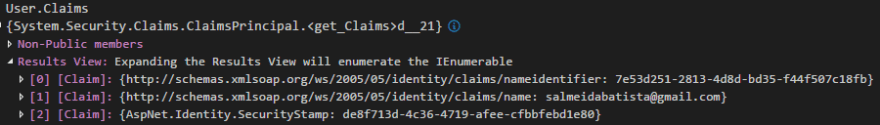
Ok, from now any controller has a property called "User" of type "ClaimsPrincipal". For example, when using in debug mode, I get all claims of a user authenticated.
If you desire, you can add others claims. Above I add a claim called "Employeer" through of object "UserManager".
Note that after create a user, through of method "CreateAsync", I am using the same object to add a claim for user.
In this sample, I am giving this attribute for user that is inserted and thus the application can validate that only the users with this attribute can access a part of system. Do you remember when I talked about authorization? Let's do now.
In order to create this authorization, we must before create our policies in C#. In Startup class, method "ConfigureServices", I insert a policy.
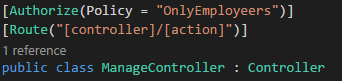
Note that I created a policy called "OnlyEmployees" and to meet this the user must have this attribute.
Created the policy, now the application can deal with authorization in the controllers. In the code below, I am using a controller called "ManageController", where only those who meet the policy can access, otherwise, the user will be redirect to other page with access denied.
Like you can see, the logic of attributes and issuers facilitate to manage users in our application.
Conclusion
The Identity facilitates to develop an application that need of user account and authorization. But before, we must know basic concepts as authentication and authorization and claims.
Did you like this article? Would you know more about .Net Core? I created a course at Udemy with a cheap price. Access https://www.udemy.com/aspnet-core-20-learn-concepts-and-creating-an-web-app









Top comments (1)
// , I don't work with .NET much, or even like it, but I love your simple explanation of the difference between authentication and authorization, Stephany.
This is gold. There's also the idea of
identity, which is just who you are, as opposed to Authentication, a process to know, or prove who you are.I've whiteboarded this so many times, and it's great to see someone who understands how these different processes fit together, and why we should discriminate among their separate purposes.