AWS Global Accelerator is a network layer service that can be deployed in front of your applications to improve its availability and performance and improve the experience of globally distributed users. With AWS global accelerator, the traffic is automatically redirected to the edge location closest to the user and then directed through the AWS global network to reach your endpoints. The endpoints can be an Application Load Balancer (ALB), Network Load Balancer (NLB), EC2 instance, or elastic IP address, and can be located in one or more AWS regions.
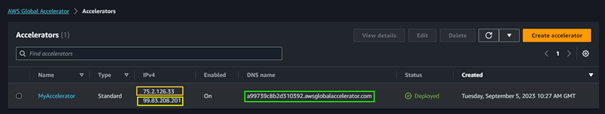
AWS Global Accelerator provides two anycast IP addresses from the AWS edge network. Additionally, it assigns a DNS name for your accelerator. These anycast IP addresses act as a fixed entry point to your app making you independent of your endpoints’ IP addresses. So, you can easily move or change endpoints without having to update your DNS configuration or client-facing applications. This makes the global accelerator a good solution for use cases that require IP whitelisting and high availability.
AWS Global Accelerator routes traffic to the healthy best-fit endpoint and in case of failure, an instant failover is provided to the next best endpoint
With AWS Global Accelerator, you can control the percentage of traffic directed to different regions using the Traffic Dial option. Additionally, you can control the traffic between endpoints within the same region using the endpoint weight option.
By default, AWS Global accelerator is protected by AWS Shield Standard for DDoS Attacks and if you need more advanced protection you can enable AWS Shield Advanced (paid)
AWS Global Accelerator is always compared to CloudFront. Both services are global and designed to reduce latency and improve performance for global applications. However, AWS Global Accelerator does not serve users from edge location caches as CloudFront does. Instead, users are served directly from endpoints, with the edge location network used solely to reduce latency. Additionally, CloudFront is limited to HTTP use cases, while AWS Global Accelerator can also be used for non-HTTP use cases such as gaming (UDP), IoT (MQTT), and Voice over IP. This makes it a good solution for a variety of applications.
In the following, I will present the main components of the AWS Global Accelerator and a hands-on based on the AWS Global Accelerator workshop.
AWS Global Accelerator components
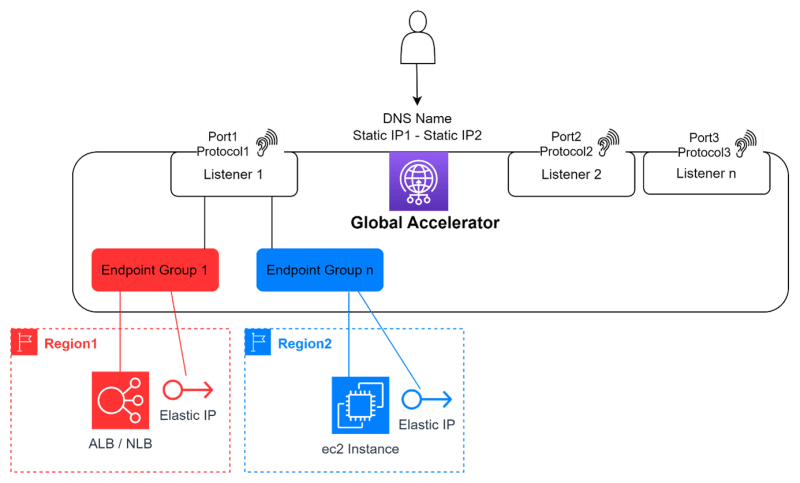
The resource that we create with the service AWS Global Accelerator is called an « Accelerator ». Each accelerator has one or more listeners that « listen » to traffic according to what you fixed as port and protocol. If there is a match between a traffic and a listener, the traffic is routed to one of the endpoints registered with this listener. The endpoints of a listener are grouped by region in an endpoint group. A listener can have one endpoint group if all endpoints are in the same region or many otherwise. Each endpoint group can have one or more endpoints. Once the accelerator is created, you receive its DNS name and two elastic IP addresses.
Let’s create an accelerator together and discover some of its features!
Hands-On — Based on the AWS Global Accelerator Workshop
I found the AWS Global Accelerator Workshop a great way to get started with AWS Global Accelerator. In this section, I share the main steps of the workshop and include some helpful images. If you are a visual person like me, I think this will be especially useful 😊.
The workshop starts with creating a basic app that does not have an accelerator. After that, the environment will be enhanced by adding an accelerator. Next, additional endpoints will be added, in the same region and in a different region. Finally, only the accelerator will be granted access to the endpoints.
Step 1. Create an app without Accelerator
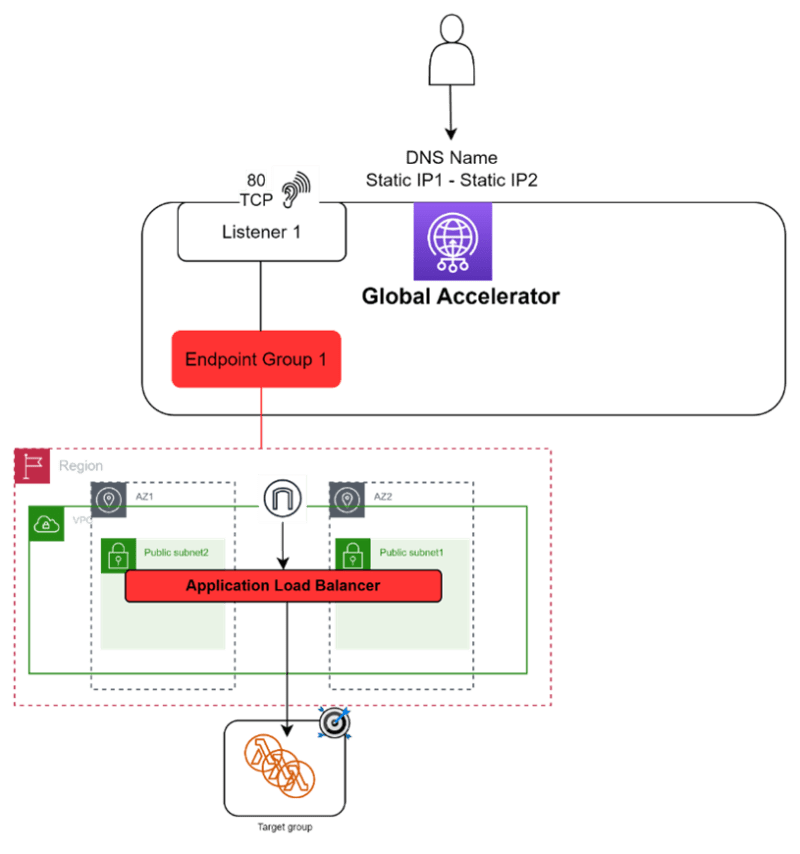
The workshop provides a CloudFormation template for deploying an environment for a simple app without an AWS global accelerator. The template creates a VPC with two public subnets in two Availability Zones (AZ), a public ALB in the two newly created public subnets, and a lambda function registered in the target group of the ALB. Additionally, the template takes care of all the necessary permissions for the lambda and the ALB. After deployment, users can access the application using the DNS name of the ALB.
In this step, you will create an AWS global accelerator to connect the user to the ALB. The accelerator has one listener that captures traffic on port 80 and directs it to an endpoint group containing the app created in Step 1 as an endpoint.
The result of this step is an accelerator with two IP elastic IP addresses and a DNS name that you can use to invoke the lambda function via the ALB
Step 3. Add another endpoint in the same region
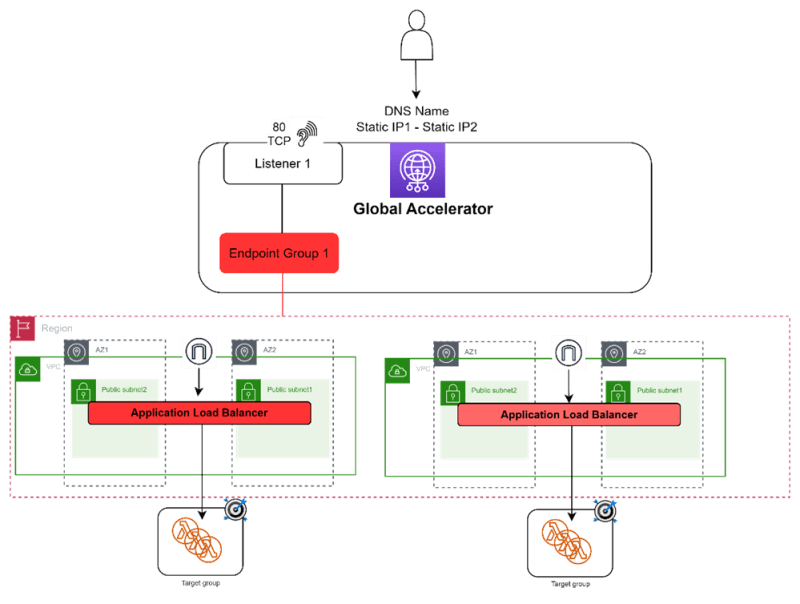
In this step, the task is to duplicate the app in the same region, so the environment now has two endpoints to serve traffic through the accelerator. In this case, the accelerator will still listen on port 80 but will now distribute traffic between the two endpoints. Since both endpoints are in the same region, the second ALB is registered with the same endpoint group that was created in step 2. To adjust the traffic distribution between endpoints, you can use the “weight” option to specify the desired percentage.
Step 4. Add another endpoint in another region
In this stage, the application is replicated in a separate region to ensure continued service for users and to be ready for potential disaster or deployment changes. As a result, we now have an additional endpoint in a different region. To connect this to the same listener established in Step 2, we need to create another endpoint group for the accelerator. With the Traffic Dial option, you can control the percentage of traffic sent to each region.
As an exercise, delete an endpoint group or an endpoint from an endpoint group and tell me how the accelerator acts as a consequence!
Step 5. Make the Global Accelerator the single internet-facing access for the app
Up until now, the security groups for the ALBs of the three apps have been permissive, allowing the user to access them via the accelerator or the ALBs. In order to increase security, we should limit access to the ALBs to only the accelerator.
How it can be possible?
When using a global accelerator with an ALB endpoint, an ENI is created in each subnet where the ALB is deployed. The created ENIs have the same security group that only allows traffic to and from the accelerator. To ensure security for the ALB, simply update its security group so that the only inbound traffic allowed is from the accelerator security group.
You can see the different ENIs created in your environment
To make it more secure, Update The ALB security groups 😊
Conclusion
AWS Global Accelerator is a good choice for global apps to reduce latency and improve user experience.
All configurations done at the level of the accelerator are transparent for users or applications that continue using the same DNS name or IP address of your app.
Don’t forget to delete resources (The three stacks created by the CloudFormation template and the accelerator) when you finish the lab!
Happy learning!









Top comments (0)