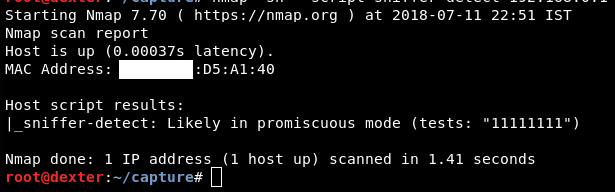
nmap -sn --script=sniffer-detect 192.168.0.102
"sn" This command is for "ping" scan, but it will not necessarily do an ICMP request.
"--script" This will tell Nmap to run a script. In this case, it was "sniffer-detect."
"sniffer-detect" This was the script name that we used for detecting the sniffer.
"192.168.0.108" This is the target network that may be compromised. In this case, this may not always work, so you can also scan the whole network by adding /24 after the gateway address. For example, in this case, it would be 192.168.0.1/24.






Latest comments (0)