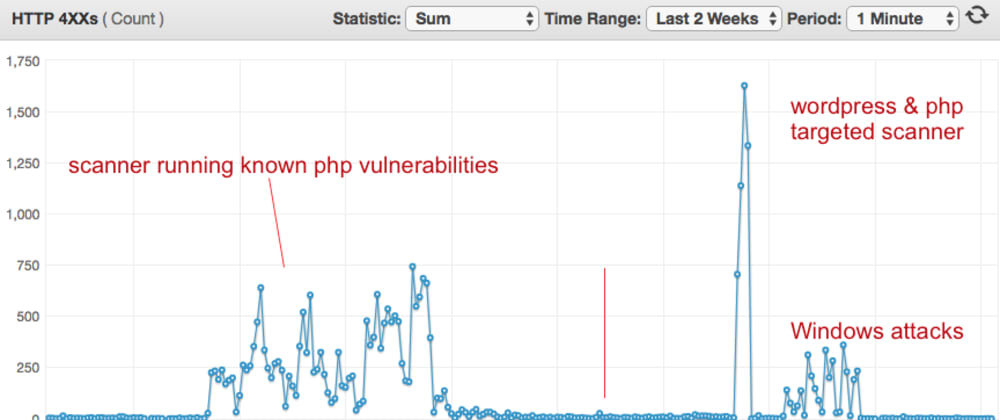
You've finished deploying your website to its new domain. You start to see your normal user traffic, but then you also notice funny patterns in you...
For further actions, you may consider blocking this person and/or reporting abuse


You need to add fail2ban to your list. An appropriately tuned
fail2bangoes a long way towards cutting down on how quickly your logs fill up with scanners and brute-forcers.Nice write-up Danny. It might also be worth talking about how things like AWS WAF can be used to prevent some of these scans/attacks.
Funny story about WAF. We had enabled it and were piping the logs to our splunk instance - a few days later we had found that WAF was dumping 300GB/day! It very helpfully drops the full request context which was great albeit a little verbose.