Certificate Management needs.
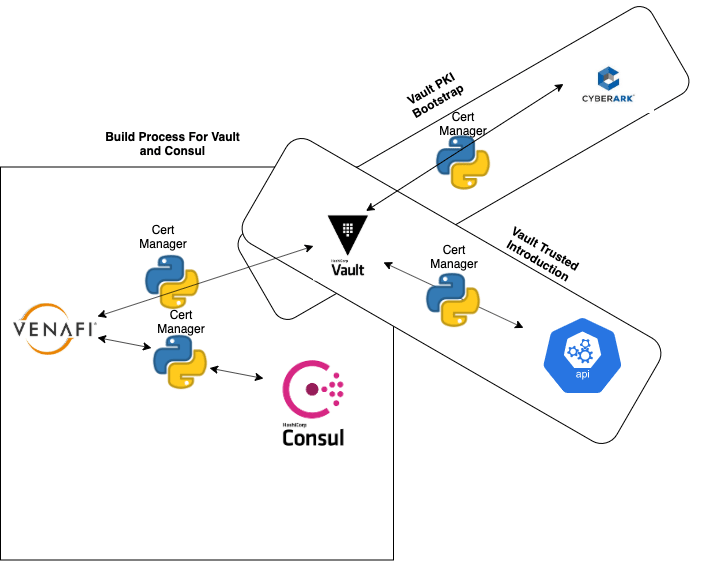
- Create and build vault backed by consul with TLS.
- Enable Vault PKI Secrets Engine.
- Use vault for client TLS auth methods.
Creating Vault and Consul using TLS - we used Venafi to create the ca-bundle, key and server cert , wrapped in python so we could install with pip and pull certs as needed.
We used a CA and private key obtained from CyberArc(storage) using the python certificate manager to enable the PKI secrets engine in Vault.
Once VAULT's PKI secrets engine was enabled, it could now be used to fetch certificates for application authentication.
This is for an on prem solution(not cloud) so we used ansible to provision consul and vault and pushing the certificate for TLS to the servers and configuring consul.conf and vault.conf.
From there we used cert manager to pull CA and private key from CyberArc and configure vault pki secrets engine(using Terraform vault provider).
For applications it was easy to request a cert from vault with the cert manger and we choose python because it could easy be turned into a pip install from git and all OS can run it successfully and allowing all applications to get the authentication they need.


Top comments (1)
// , Does this require any plugins for Vault or Consul?
Also, in case this was used in AWS or GCP, could I use an S3 bucket or GCP Cloud storage, respectively, instead of CyberArk? Why is that part of the step needed for pulling a CA and private key, anyway?