What is Amazon ECR?
A Container Registry is a centralized way to distribute and manage container images. Amazon ECR is simply a container registry that AWS provides, and you can create public and private images, just like on Docker Hub.
Why Amazon ECR?
Ecosystem
Some teams prefer to keep all their services in the same ecosystem. In this case, AWS can make things much easier to manage and control user access. For example, you can use ECR instead of Docker Hub or Amazon Elastic Container Service (a fully managed container orchestration service) instead of Kubernetes (the de-facto standard for container orchestration). Instead, you can use Kubernetes on AWS with Amazon Elastic Kubernetes Service.

Rate limits
There is at least one other reason to use ECR, if your team uses free Docker Hub, you might run into rate limits while pulling images into something like AWS CodeBuild. The rate limit is set to 100 pulls per 6 hours per IP address if you are anonymous and 200 pulls per 6 hours for authenticated users with a Docker ID.

The cheapest way to overcome this might be to add the image to your AWS accounts ECR and use that instead.
Creating the ECR Repository
You can create an ECR Repository manually in the ECR console, but we will focus on the CloudFormation method.
You can create a file called ecr.yml and paste the template below inside it:
AWSTemplateFormatVersion: "2010-09-09"
Description: >
This template creates ECR resources
Parameters:
IAMUserName:
Type: String
Description: IAM User Name
Default: "YOUR_USER_NAME"
AllowedPattern: "[a-zA-Z0-9-_]+"
ConstraintDescription: must be a valid IAM user name
Resources:
ECRRepository:
Type: AWS::ECR::Repository
Properties:
RepositoryName: !Ref AWS::StackName
RepositoryPolicyText:
Version: "2012-10-17"
Statement:
- Sid: "AllowPushPull"
Effect: Allow
Principal:
AWS:
!Join [
"",
[
"arn:aws:iam::",
!Ref AWS::AccountId,
":user/",
!Ref IAMUserName
],
]
Action:
- "ecr:GetDownloadUrlForLayer"
- "ecr:BatchGetImage"
- "ecr:BatchCheckLayerAvailability"
- "ecr:PutImage"
- "ecr:InitiateLayerUpload"
- "ecr:UploadLayerPart"
- "ecr:CompleteLayerUpload"
Outputs:
ECRRepository:
Description: ECR repository
Value: !Ref ECRRepository
The above template is responsible for creating the repo and proving an IAM user, specified in the YOUR_USER_NAME parameter, the necessary permissions to use the repository. Please replace YOUR_USER_NAME with your actual IAM username, or the creation will fail.
To deploy the template, run:
aws cloudformation deploy --template-file ecr.yml --stack-name ecr-repository --capabilities CAPABILITY_NAMED_IAM --profile default --parameter-overrides IAMUserName=YOUR_USER_NAME
and you will get an output similar to this:

You can check the status of the stack creation by running
AWS cloudformation describe-stacks --stack-name ecr-repository
If it created successfully, you should get an output similar to this with a StackStatus of CREATE_COMPLETE:

You can also check on the CloudFormation console in the region your default profile is set to.

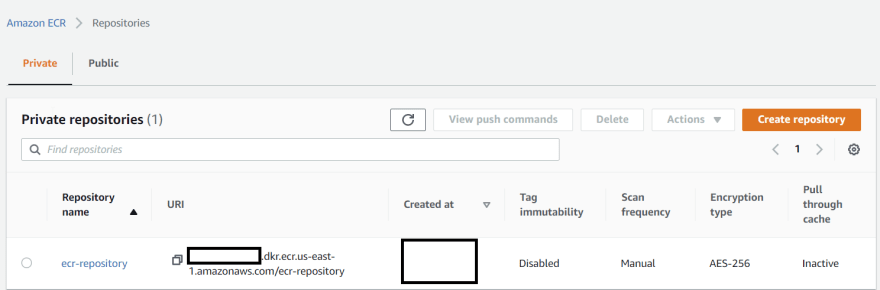
Then in the ECR console, your repository should be there.
Cleanup
Always clean up resources you don't need to avoid unexpected bills.
To delete to the repository, run:
aws cloudformation delete-stack --stack-name ecr-repository
Confirm the delete was successful by checking the status of the stack,
AWS cloudformation describe-stacks --stack-name ecr-repository
and you should get a response similar to this

You can double-check in the AWS console to be sure.







Top comments (0)