This is my first time at DevNexus 2020, and I'm taking notes as I attend the talks.
Table of Contents
- 10:20am: Reactive Microservices in Action by Emily Jiang
- 11:20am: Runtime Security for Containers by Spencer Krum
- 1:10pm: Introduction to TensorFlow.js by Gant Laborde
Reactive Microservices in Action
Emily Jiang, Java Champion, STSM, IBM @emilyfhjiang
Liberty Microservice Architect, Advocate
Senior Lead for MicroProfile and CDI
Goal of this talk: when people talk about Reactive, you’ll know what they mean. Reactive isn’t for all use cases and scenarios.
Emily comes from an imeritive programming background, where you’d create microservices making synchronous calls between themselves. As an example, if a user’s browser makes a request to microservice A that in turn hits microservice B. You can use asynchronous calls so that your first microservice A doesn’t have to wait until B completes.
However, microservices are like kids, they need guidance and contingency plans. Sometimes they return correctly, sometimes they time out, sometimes they error. We have microProfile Fault Tolerance. Fallbacks allow you to take different actions depending on the circumstances of the call completion.
Microprofile Context Propogation: We want to capture the context when one microservice calls another. We can use ThreadContext to do this: threadContext.withContextCapture(). Using this, the context of the request can be provided to the new thread.
Note: Most asynchronous things aren't non-blocking. The solutions above don't solve a blocking issue. Once you've used up all the threads in your system, you can't do any other operations. Long-running operations mean all the threads are blocked; you're not fixing the problem, you're just hiding it.
You need async + non-blocking to use resources efficiently.
Reactive: You need to care about reactive when you don't know who your I/O consumers are. Reactive surfaces in lots of programming contexts. If you've heard of reactive programming, you've probably used it at some point. Reactive extensions help developers deal with reactive programming, streams type and operators, data streams and propagation of changes.
Reactive Streams in J9+: Subscribers can subscribe to a Publisher. Subscriber implements onSubscribe, onNext, on Error and onComplete. A Subscription can request() items, and cancel.
With microservices, applying reactive principles allows temporal decoupling and back-pressure policies.
Do not always try to achieve 100% reactive systems; it's not always reasonable, and you need a lot of specalized tools to make a partially reactive system. Read reactivemanifesto.org for more information. Reactive systems must be message-driven, resilient, elastic and responsive.
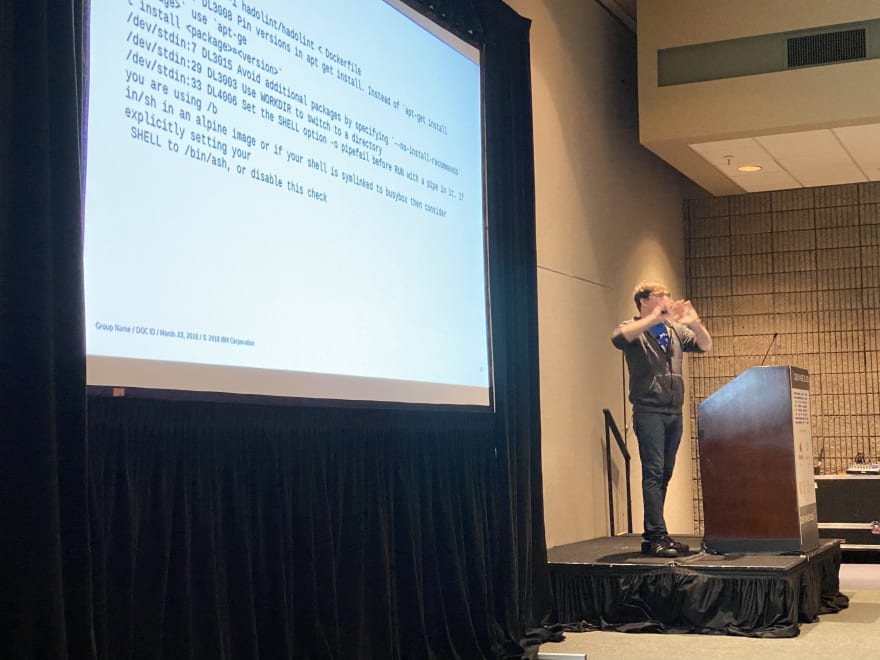
Runtime Security for Containers
Spencer Krum, Developer Advocate at IBM @nibalizer
In this talk, Spencer covers how to implement runtime security for Kubernetes using the open source project Falco.
We're not just consuming big chunks of code, we're also consuming small chunks of code. When you look at a package dependency graph, you have a huge coverage of code. When you're using npm or ruby gems, you're pulling down software that all runs on its own cycle. SNYK is a company that scans everything in your dependency tree and gives you a report of low/medium/high vulnerabilities you're exposed to.
How do containers complicate the picture? Developers can, in seconds, bring in an ML workload that are on docker images with python code that are based on xyz... back in the day, we had one VM image and changes would be applied globally, but these days it's much harder to stay consistent. There is no steady state from which to reason and test.
Also, these days we'll have dynamic workloads, and pods that are running today may not be running tomorrow. Open source has given us the ability to pull in and consume more software faster, which is great but is also a risk.
We want to add security at three locations: between development and testing (when the application is built,) testing and deployment (when the images are being built,) and during monitoring.
"Containers make everything harder because everything is more numerous and more ephemeral." A new kind of speed an diversity in your production environment requires new tools, including Falco, which is what this talk is about. It's a runtime security tool, open source and in the CNCF incubating phase. You can join Falco's slack, which is fairly active, for more info.
Falco can consume data from the Kubernetes audit log as well as the kernel module and eBPF probe. We also feed in all the rules and configurations. After filtering, we have a number of outputs: An alert system, slack, database and gRPC.
eBPF is "extended BPF" based on a project from 1992. It's kind of hard to get started as it's a very low level thing that also surfaces really cool insights about higher level applications. Brendan Gregg has a book called BPF Performance Tools, and there is another book called Linux Observability with BPF that is a good read if you'll be using eBPF.
Introduction to TensorFlow.js
Gant Laborde (@GantLaborde) is a CIO of Infinite Red, React Native core contributor, and GDE in Web and ML.
Back in the day, if you coded a tic-tac-toe algorithm where the computer chooses the next space to fill, that was considered AI. Machine learning is the practice of having the algorithm define what it should do based on the data it encounters. You can run the machine, come back later, and it's gotten really good at solving that problem.
Why Machine Learning? If we taught an algorithm to read books and discern proper grammar based on the text of a thousand books, you may be able to train the same program on different languages based on different data sets (a thousand books in a different language.) It's the power that comes from machine learning, which developers can access that today.
In 2010, Google had less than 10 machine learning models in production. By 2017 they had over 4,000 production machine learning models.
We can do: Deep Fakes, Region Detection, Style Transfer. Example, Crisp.ai removes extraneous background music from your video calls. There's a YouTube channel of AI-created heavy metal based on a library of heavy metal songs. Other examples: Deoldify, parking space detection.








Top comments (0)