Container registries have become an essential part of our (work) lives with the increasing usage of various containers, and container management tools, used in our CI/CD processes. As developer and DevOps enthusiasts, we surely find the need to have a registry that can be robust and scalable according to our needs. It is also requisite that the access to these registries is in accordance with our business use cases.
Using the JFrog Container registry, here’s how we can have our public and private repositories segregated and managed using the basic permissions model.
Public repositories
The public repositories are the ones that can be accessed by anyone in our organization regardless of the team they belong to. To make them public, all we need to do is to enable anonymous access generally (Under Admin-> Security Configuration) and give the user ‘anonymous’ appropriate permissions to these repositories or builds that use these public repositories.
Step 1: Enabling anonymous access to the instance

Step 2: Allocating appropriate resources (repositories/builds)
Step 3: Giving the user ‘anonymous’ required permissions to the resources
Private repositories
The private repositories are the ones that are being utilized by a particular user/team or a group of teams in your organization. The access to these repositories can be based on the teams - groups, or users.
To give pertinent role-based access control to these repositories, we just need to allocate users or groups apt permissions to these resources (repositories/builds) based on the use cases.
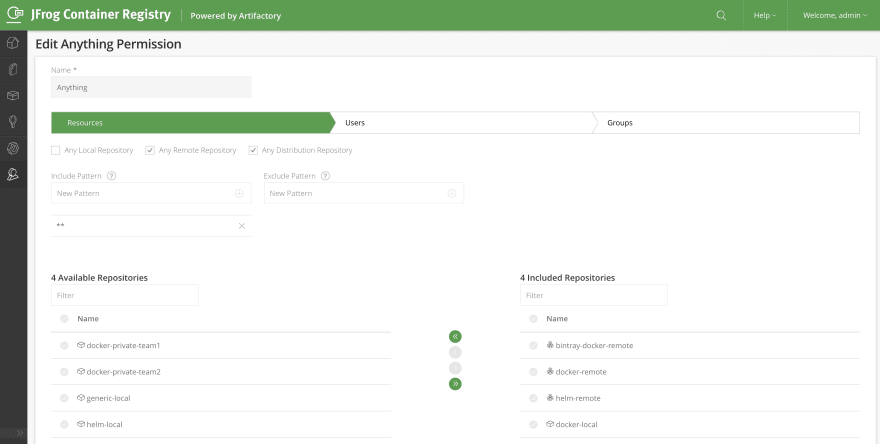
Step 1:Include the relevant resources (Private repositories/Builds) in a Permission Target

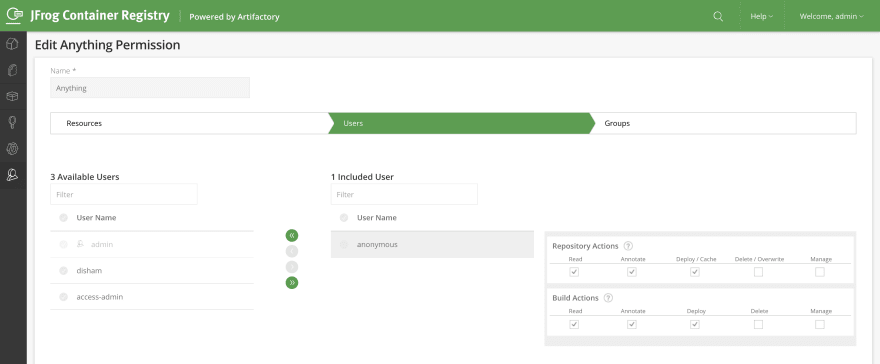
Step 2: Give apt permissions based on the Business use cases (Team-based permissions)

Additionally, the users of a registry can authenticate using LDAP integration as the JFrog Container Registry is powered by Artifactory. These users can then be set up to have different permissions/groups in the Registry instance based on the Permissions model of the organization.
In this way, managing all of your public, as well as private registries, can be easy and secure with a Container Registry that you can always trust.


Top comments (0)