I have recently come across several new terms in the security space. This article attempts to explain some of the security terms such as OAuth2 / OpenID Connect.
What is OAuth2?
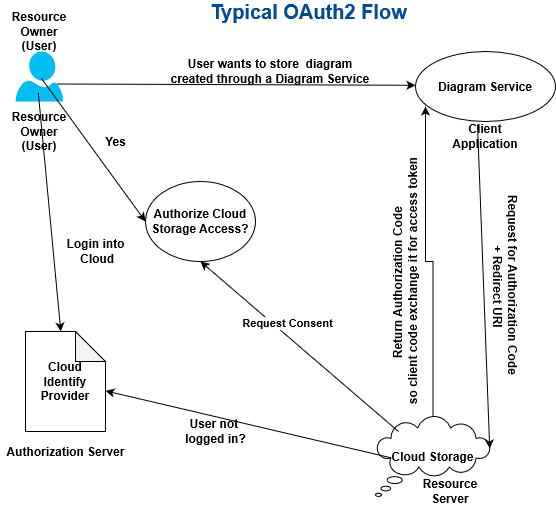
OAuth2 is a security standard where a user gives permission to one application to access a resource on their behalf in another application. OAuth2 is mainly used for authorization. OAuth2 could be better explained with below scenario.
Scenario: User creats a diagram using a drawing service application and wishes to store the created diagram in a cloud storage.
Let’s walk through the steps involved in this process in OAuth2 terms.
- User (resource owner) created a diagram in the diagram service application (client).
- Chooses to store the file in their cloud storage (resource server).
- Client application tries to access the user’s cloud storage drive on user’s behalf.
- Cloud storage first tries to identify the user that is trying to authorize storage permission.
- If the user is not already logged into the cloud storage service, cloud storage service first makes the user login into their service (authorization server).
- Then cloud storage checks with the user to see whether they want to authorize (consent) the drawing service to access cloud storage.
- Once authorized, the user is redirected back to the drawing application and successfully saves the diagram in the cloud storage.
- Important point to note is that the diagram service application only has been authorized to only specific folders of user's cloud storage.
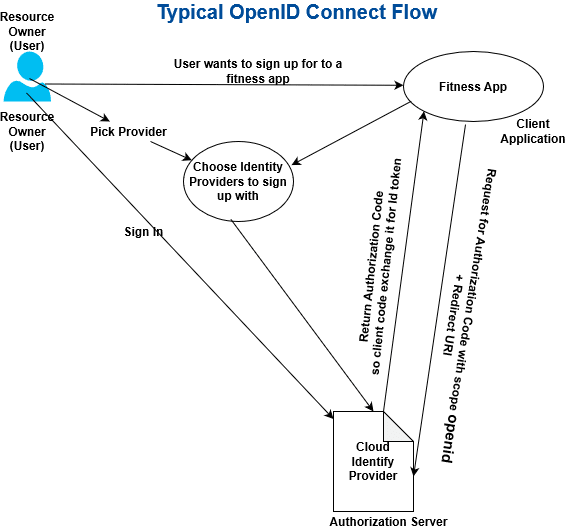
What is OpenID Connect (OIDC)?
With OAuth2, client applications can perform specific actions on user’s behalf but applications do not have provision for getting information about the user. OAuth2 standard mainly solves the problem of authorization not authentication. People wanted to use a similar approach for authentication. The OpenID Connect standard was invented to address authentication. OpenID Connect is a thin layer that works on top of OAuth2.
Scenario: Let's consider a scenario of a user trying to sign up for a fitness app (client application):
- Client application presents the user with a list of options of already existing identity providers.
- The User gets to pick one of their pre-existing identity providers such as Google, Facebook, or Github to sign up with the new fitness application.
- With this mechanism, the user does not have to create and maintain a new set of credentials to sign up for the fitness app.
- With OpenID Connect, client applications could identify the user and get their public user profile data to successfully authenticate the user into their fitness app.
Glossary:
Resource Owner: User is the owner of their identity, they get to decide any action that can be taken on their behalf.
Client: Target application trying to get access to the user’s profile or wants to perform action on user’s behalf (diagram service application).
Authorization Server: The application that knows the resource owner.
Resource Server: The API or service the client wants to use on user’s behalf (cloud storage).
Redirect URI: The URL of the client application to which user will be redirected to from the authorization server after granting permission to the requested resource.
Response Type: The type of information client expects to receive. The most common response type is code where the client is presented with authorization code.
Consent: The authorization server takes the scopes the client requested and verifies with the resource owner whether or not they want to give permission to the client.
Client Id: The id used to identify the client with the authorization server. This id may be visible through the browser while exchanging code.
Client Secret: This is the secret code generated by the authorization server for the client access. Should be kept securely by the client application. Client applications use client with secret during access token or Id token exchange for authorization code.
Authorization Code: Code sent by the authorization server to the client application. It is a short lived code and has to be exchanged for access token or Id Token depending on the need of the client application.
Access Token: Access token is similar to a badge. With access token client application can access user’s resource from the resource server.
Id Token: In Openid, authorization code could be exchanged for Id token that identifies the user trying to authenticate into a client application.
JWT: JWT stands for JSON Web Token. JWTs are encrypted Id tokens that are exchanged between authorization server and client application.






Top comments (0)