Ledger vs Trezor: Best hardware wallet to secure cryptocurrency
In this article, we will compare Ledger vs Trezor based on multiple criteria and help you decide which is the best hardware wallet suited for your need.
What are hardware wallets?
Hardware wallets are physical devices that store cryptocurrencies. They contain private keys in an offline mode and cannot connect to the internet or run complicated apps, hence, safe from attacks.
Therefore, they are also known as cold storage (or cold wallets). Hardware wallets are compatible with several interfaces and apps and support multiple cryptocurrencies. They are also compatible with other third-party wallets that act as an interface to manage coins.
Always remember, the more complex the device is, the greater is the chance of it getting attacked. These wallets have a minimal and simple design, reducing the overall attack surface.
How do hardware wallets work?
Hardware wallets only sign transactions. Therefore, in order to prepare the transactions and broadcast them to the network, you need to use another device (ex- laptop) that is connected to the internet.
Usually, you need to download a program to interact with the hardware wallet because these wallets allow only specific types of information such as transaction data.
To start the transaction, we need to enter the pin(password) in the hardware wallet. Always make sure that the transaction we are approving on the hardware wallet’s screen is the same as the connected device (Laptop).
You should always remember the seed phrase, which is a 12- 24 words combination that is given to us to initialize our hardware wallet. Anyone who has access to the seed phrase can access your cryptocurrencies, therefore you must keep them offline in a secure place.
Ledger vs Trezor: Physical Appearance
Display
Both the Trezor and the Ledger wallets have a display screen. They are used to display the seed phrase and send cryptocurrencies. Trezor has a larger display screen compared to Ledger, thus making it more convenient to view. However, Trezor Model T also has a nice color touchscreen.
Material
Trezor wallet is made from plastic, while the Ledger wallet comes with a stainless-steel body. The stainless steel makes the Ledger wallet more durable and portable, giving it a more stylish look.
Buttons
Both the devices come with two buttons that are used to manage their software. It is important to note here that Trezor’s buttons are easier to use since they have a good amount of space between them. The buttons in the ledger wallet are very close to each other, increasing the risk of pressing both at once.
Size
Trezor is bigger than the Ledger Nano S. Therefore it may be easier to carry the Ledger wallet with you because of its smaller size.
Ledger vs Trezor: Cryptocurrency support
It is very important to know what coins are supported by both wallets. Currently, both Trezor and Ledger wallets support 1000+ coins. Both wallets support all ERC20 tokens on the Ethereum network.
Ledger vs Trezor: Open source
Ledger
The Ledger wallets run their own custom operating system BOLOS. This means that we cannot see what code goes into the device and the firmware that it runs on. However, the specifications are completely open and detailed, and all cryptographic operations are deterministic, allowing it to have the required information.
Trezor
The Trezor wallets use open-source firmware and software. Using an open-source has both pros and cons. The bugs can be identified easily but it comes with an attached security risk.
You can learn more about Trezor on its GitHub .
Ledger vs Trezor: Supported OS
Trezor and Ledger are compatible both with computers and smartphones. The supported operating systems are Windows 10, macOS 10.11, and higher, Linux, and Android OS.
Ledger supports Windows 8+, macOS 10.10+, Linux excluding ARM Processors. It is also compatible with Android 7+ smartphones.
Ledger vs Trezor: Difference in password encryption
Both Trezor and Ledger wallets have a password function. Each different passphrase unlocks a unique set of accounts. We can use multiple passphrases.
These settings are useful to have one main account and two or more hidden accounts from the same wallet, with the same 24 words recovery seed. So regardless of whether we have the recovery seed, we cannot access the corresponding wallet without the password. If you have to forcefully give your password, you can always give the one which has fewer assets.
In Trezor wallets, this password is entered via a connected device such as a Laptop, making it vulnerable for attackers to read it.
However, in Ledger wallets, the password is linked to another PIN which is entered using the normal keys.
Trezor wallets have a password manager that works with Chrome and cross-platform on your MacOS, Windows, and Linux. We can install the Trezor Password Manager Chrome extension (TPM) and sign in with Google Drive or Dropbox. We can also connect our Trezor device by entering our PIN and then enable Password Manager on our Trezor device.
Ledger vs Trezor: Compatibility with other apps
Ledger
The Ledger wallet is compatible with apps such as Ledger Live, Electrum, MyEtherWallet, Copay, Mycelium, Electron Cash, GreenBits, MyCrypto, Binance, Magnum, etc.
Trezor
The Trezor Wallet is compatible with apps such as MyTrezor, Copay, MultiBitHD, Magnum, GreenBits, Electrum, Mycelium, MyEtherWallet, etc.
Both of the wallets are compatible with a large number of apps and have a lot of those apps in common. So always choose, depending on what you need.
Ledger vs Trezor: ** Hardware**
Ledger
The ledger wallet has a very distinctive hardware architecture, consisting of a very secure Operating System BOLOS (Blockchain Open Ledger Operating System), and specialized chips known as Secure Elements.
In order to utilize the Secure Element’s unique security capabilities while being able to manage the different peripheral devices, the Secure Element has been provided with a STM32 microcontroller (MCU) which acts as a router between the peripherals and the Secure Element and notifies it whenever new data is to be received.
The Secure Element is responsible for executing all of the applications of the BOLOS environment.
Trezor
CPU: The processor used by a Trezor is an ARM Cortex-M3 processor @ 120 MHz, while the software is custom.
Screen: The screen is an important tool, which enables the users to verify the authenticity of the data entered. The Trezor One uses an OLED screen (128 x 64 pixels); while the Trezor model T uses an LCD touch-screen (240 x 240 pixels). Both of the screens provide ample of space on the screen so as to display the warnings, requests, images, or transaction details. It is also used to display the recovery seed of our private key.
Buttons: Two buttons are used by Trezor One in order to receive confirmation from the user. Physical confirmation is important in order to protect the accounts from attacks.
Trezor model T also uses a Micro-SD card slot and a USB-C Connector.
Ledger vs Trezor: ** Security**
When considering the security in entering our passwords, in Trezor wallets, the password is entered via the keyboard of the connected device, making it vulnerable for attackers to read it.
However, in Ledger wallets, the password is linked to another PIN which is entered using the normal keys.
How to check if your Trezor or Ledger wallet is tempered with?
There are two ways in which the device could be attacked physically. First, it could be compromised before we receive it. To avoid that, the Trezor uses tamper-evident seals. They are sealed using industrial glue and putting that back again after making changes to the hardware is quite difficult, so we come to know that the wallet has been compromised if it has a damaged or a broken seal.
Ledger uses a trusted computing base which is validated using cryptographic proofs. Users can verify the integrity of the device by performing an attestation check. They also prevent evil maid attacks.
When to do when Trezor or Ledger wallet is stolen?
These devices are protected by a pin and after three unsuccessful attempts, it wipes off all the contents, self-destructs, and locks the suspicious user out.
Both Trezor and Ledger are by design protected from remote attacks. They do not connect to the internet directly and when they are connected to an internet-enabled device, they only pass necessary information like the transaction details.
While both Ledger and Trezor are highly secure in their own ways, Trezor is considered to be a better option as it is more secure because of its open-source feature.
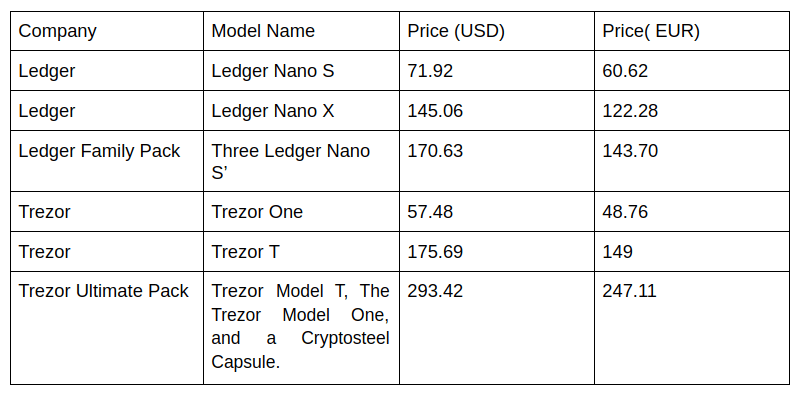
Ledger vs Trezor: Pricing
Ledger vs Trezor: ** Models**
Both Ledger and Trezor come with two models. In this section, we will compare their own models with each other.
Ledger Nano S vs Ledger Nano X
The Ledger hardware wallet consists of the following models:
Ledger Nano S
The Nano S was the predecessor of Nano X and was developed in 2014. It is made of steel and consists of the ST31H320 Secure Element and theSTM32F042K microcontroller chips.
It is a bit lighter and smaller than the Nano X. It consists of a smaller screen with a display size of 128 x 32 pixels and has two buttons on one side of the device.
It does not consist of a battery of its own since it supports only wired transactions and comes with a micro USB Type B.
Ledger Nano S is not exactly devised for mobile transactions and rather requires access to a computer to perform transactions. It does not have a lot of storage space and can accommodate not more than 10 apps.
Because of its comparably cheaper price, the Nano S still remains a popular choice among cryptocurrency enthusiasts and novice traders.
Ledger Nano X
Ledger Nano X is Nano S’ successor. It is made up of steel and consists of theST33J2M0 Secure Element and theSTM32WB55 microcontroller, which are wireless chips and have in-built Bluetooth support.
Nano X is a bit heavier and larger than the Nano S. It has a larger screen than the Nano S with a display size of 128 x 64 pixels and allows for more room for displaying information.
It consists of two buttons that are placed on either side of the device which feels more durable and more convenient to use.
Ledger Nano X is supported by a 100 mAh rechargeable battery. comes with a USB Type C Connector. It provides us with a lot more storage and can accommodate more than 100 apps easily, with each of them supporting a different crypto-currency. Ledger Nano X is a much more popular choice among professionals who need to access their funds anytime and anywhere.
Trezor One vs Trezor model T
The Trezor hardware wallet consists of the following models:
Trezor One
The Trezor One was the first-ever Trezor hardware wallet to be developed by SatoshiLabs.
It has two push buttons and a 128 x 64-pixel OLED display rather than a touch-screen. It resembles a keychain and is very compact and light-weight to carry around.
Trezor One is protected by an ABS plastic case, which is impact-resistant and robust and protects against minor physical damages to an extent.
It consists of a STM32 F2 microcontroller and the ARM Cortex-M3 processor running at 120 MHz, which provides smooth and secure access to our funds.
The Trezor One as well as the Trezor model T comes without a battery.
Both the Trezor wallets allow various features like Password Manager (which enables us to store, access, and manage login details for various apps) and U2F authentication token (which allows an easy login to various social media sites like Twitter, Github, Google, etc).
It is an ideal choice for a hardware wallet with low budget conditions.
Trezor Model T
The Trezor T is a second-generation wallet and is the newer, updated, and more secure version of the Trezor One hardware wallet.
It has a newer, faster, and better Operating system and processor. It is protected by an ABS+PCplastic case and consists of a STM32F4microcontroller and the ARM Cortex-M4 processor running at 168 MHz.
Trezor Model T consists of a 240 x 240 pixel RGB color display with a touch screen and supports a lot more crypto-currencies than Trezor One.
The touch screen provides the user with a more user-friendly experience, better accessibility, and ultimate control of the hardware wallet.
The screen is the only medium to enter the passphrases or PIN, unlock the device, to recover existing wallets, and to confirm other actions, which makes it less prone to cybercrime and more secure during the seed recovery process.
The screen also has a bigger size which makes the wallet much more convenient to use.
The wallet has built-in mobile connectivity, an SD card slot, and a USB Type C Connector, which enables mobile transactions, and is compatible with any mobile device or computer. Rather than having to use third-party interfaces, the wallet allows us to use its own web-wallet interface for the ERC20 tokens transactions.
Hardware Wallet Advantages
There are multiple advantages of using hardware wallets:
- Hardware wallets are capable of hosting multiple crypto-currencies at the same time in an isolated, offline environment.
- These wallets are more secure and less vulnerable to computer viruses and malware, which ensures a more secure transaction.
- Hardware wallets are protected by an encrypted pin, which is generated by us. After the three consecutive wrong password entries, the wallet self-destructs and locks out, anybody who tries to forcefully enter by trying different pins. The keys would be deleted by the device in order to keep our funds secure.
- The private key is entered only on our encrypted hardware device, which makes it unexposed to other people and devices and prevents it from getting hacked.
- These wallets do not allow anybody to make any transaction without having access to the device, since the transaction verification is done by the hardware wallet itself. Thus, our data and transactions are safe as long as we are the only ones having the access to the hardware wallet.
Hardware Wallet Disadvantages
The disadvantages of hardware wallets are as follows:
- They are not free.
- The wallet could get lost or broken.
- The private key extraction becomes quite difficult.
- Since they are highly secure, they don’t allow us to perform a transaction in just a few clicks and it is sometimes difficult to set up the wallet.
- There are a lot of people and online shopping platforms that are involved in manufacturing and selling fake hardware wallets, which could end up emptying our funds.
Also, Read
- The Best Bitcoin Hardware wallet
- The Best Crypto Trading Bots
- The Best Crypto Tax Software
- Best Crypto Trading Platforms
- Best Wallet for Uniswap
- Best Crypto Lending Platforms
- Top DeFi Projects
- Bitsgap review — A Crypto Trading Bot That Makes Easy Money
- Quadency Review- A Crypto Trading Bot Made For Professionals
- 3commas Review | An Excellent Crypto Trading Bot
- 3Commas vs Cryptohopper
- The Idiots Guide to Margin Trading on Bitmex
- The Definitive Guide to Crypto Swing Trading
- Bitmex Advanced Margin Trading Guide
- Best Crypto APIs for Developers
- Crypto arbitrage guide: How to make money as a beginner
- Top Bitcoin Node Providers
- Best Crypto Charting Tool












Top comments (0)