Many large companies use to implement strict rules for accessing servers hosting their applications. One of the security measures some of them implement is to place a gateway between "you" and the server you need to access. This gateway is also known as Jump server, Jump host, or Jump box.
A typical implementation of this requires you to, firstly, open an SSH connection to the Jump host with your own credential and, secondly, from the inside of the Jump host, open a second SSH connection to the actual server you need to access with another account (usually a non-personal account which can be the user used to deploy and run your application).
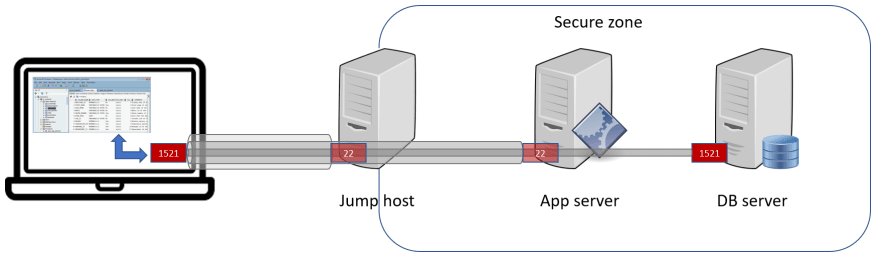
Let's suppose that you work in a company like this and that you want to create an SSH tunnel to port 1521 of an Oracle Database Server which is only accessible from your application server. What you need to do is to create an SSH tunnel like this:
The following command creates this SSH tunnel via the Jump host (you will be prompted for the users' password):
$ ssh -v -N appusr@appserver -J myusr@jumphost -L 1521:dbserver:1521
With this command, you are tunneling the port 1521 of localhost to the port 1521 of dbserver.
In other words, you are firstly doing an SSH connection to jumphost with user myusr, then another SSH connection to appserver with user appusr, and finally forwarding port 1521 from localhost to dbserver.
This command is being executed in verbose mode (-v), which is useful for debugging, and not returning the shell prompt of the appserver but just forwarding the port (-N).
After this, you can then use your preferred SQL client tool to connect to the remote database server as if it was running on localhost:1521.






Top comments (4)
We've a similar setup at my workplace. And due to that, for the longest time, we've had to connect to the database and run commands over the terminal. As most database clients such as MySQL Workbench and Robo 3T don't support such a setup for connection.
Only recently has DBeaver added support for connecting to the server through a jump server.
One of my friends had suggested that I would need to set up an SSH tunnel between my machine to the jump server, jump server to application server and application server to database. So I tried to learn about it but most articles and examples I found online only showed a single level tunnel with no jumping.
So I was pretty lost.
I'm now able to successfully create a tunnel to the database. So thanks a ton!! :)
If possible, can you point me to more resources related to this?
I am using windows server.
How can i configure this command on Putty/Kitty?
In case of Windows, it would be ideal if you install Cygwin or WSL (Windows Subsystem for Linux, available on Windows 10). You are going to find a way to install ssh command on these two options.
If you really wanna use Putty, you can still do it, but it will be a bit more complicated as it will require you to explicitly open two distinct SSH sessions: one via Putty and the other via ssh command on the
jumphostserver.For the sake of simplicity, I'm gonna use the same example used in the article.
1. Your Putty SSH session
You will need to configure an SSH session to the
jumphostserverAnd set up a tunnel, mapping your local port
1521to the port1521of thejumphostserverUse this Putty session to log in to the
jumphostserver with usermyusr2. The second SSH session (via command line)
Once you are connected to
jumphostserver, you can now create the second SSH session to connect to theappserverand create a tunnel from thejumphost's local port1521to the port1521of thedbservermachine.You will be prompted to provide the
appusr's password.3. And it's done!
Now, you are ready to connect to the "behind-the-jumphost" database server via port
1521oflocalhost.Oh my gosh! This response seems to be almost as extensive as the original post :-p
Take care and be healthy!
Many thanks for your advice and your time