Streaming service accounts get compromised all the time either due to data breaches, credential stuffing attacks from leaked databases, or simply because of users employing weak passwords.
How accessible a streaming service makes it for a rightful account owner to attempt recovery is what counts.
However, in the case of Hulu it may not be so simple, especially when a compromised account is too old, and let me explain why.
Yes, it happened to me (shame!). An ages-old disposable Hulu account I hadn’t used since college days, and which was setup with a lax password to trial the service, got compromised in January 2020. Personally, I didn’t care that much as this was a throwaway account to begin with, but it’s still better to keep what’s yours to yourself, so I attempted a recovery.
Not only had the attacker changed the account’s password, but additionally changed the email address linked to the account.
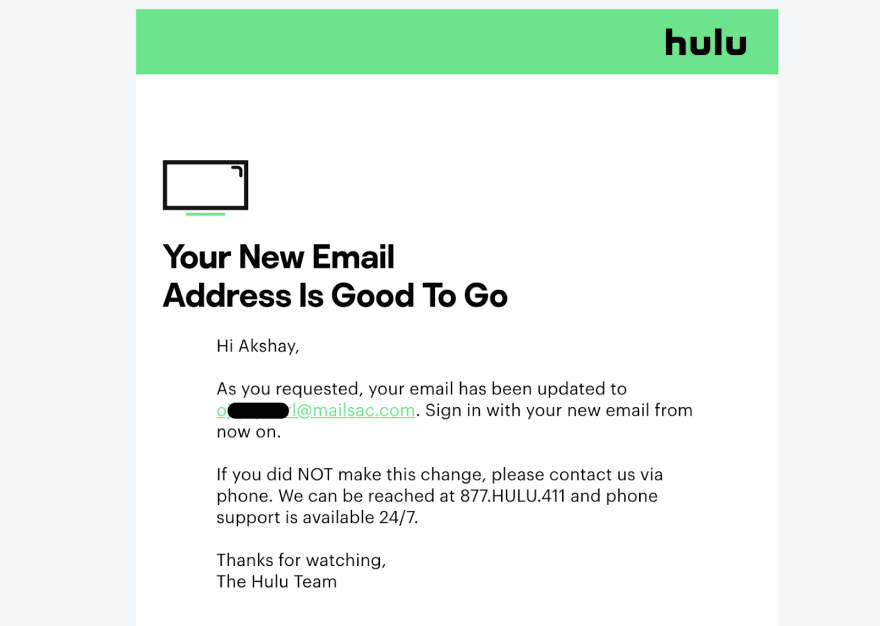
Image: Hulu sends out email alert when account email is changed (Source: Security Report)
Now, to be fair, Hulu did send out a security notification to the original email address informing me of the change, along with the “new” (attacker’s) email. Hulu’s recommendation was to call the 877 number to attempt an account recovery, “if you did not make this change.”
Mind you, calling U.S. toll-free (800 or 877) numbers from outside the U.S. can be incredibly painful. As of January 2020, which is when the account got compromised, I was no longer living in the U.S.
Once I did manage to get to the number via a VoIP phone, it had 30+ minute wait times at the time. After dialing on multiple occasions and eventually giving up on long hold times, I tried to find alternate means of contact: such as a web chat or ticketing system.
In what can be described as a catch 22, Hulu Help form requires you to log in first before contact with support can be initiated. Granted the security feature prevents unauthorized changes for existing users, it does nothing to help users whose accounts have already been hacked.
Image: Hulu Help online form requires a login first prior to initiating contact with support
Naturally, because the email address was changed to the attacker’s, a “forgot password?” link wouldn’t work. So contacting support via the online help form wasn’t an option.
Hulu also offers a “forgot your email” feature too but with a caveat: it requires your Hulu billing information. But in the event of account compromises like this one, the email has already been altered to the attacker’s, so how could this help?
Also, if the account is exceptionally old, was using a PayPal billing agreement, or is a “cancelled” account (from a billing perspective) the user’s credit card information, even if they can readily locate it, would no longer be applicable.
Image: Hulu forgot email form requires user’s billing information associated with the compromised account.
The question remains, what happens if the user is indeed able to locate their billing information for an account, but it still doesn’t work?
Email changed twice?
Could it be the attacker had removed the associated “card on file” or changed it to theirs? Or better yet, changed the email at least twice in a row so as to purge your original email from Hulu’s systems, along with the “newly set” attacker’s email (o*****l@mailsac.com) that Hulu notified the victim of, via a courtesy email.
This would leave no viable way for the user to identify themselves to Hulu, unless Hulu support staff has visibility into every such logged event.
In that case, what other option does the user really have other than being indefinitely locked out of their account?
When the user calls Hulu and does manage to get through their long wait times, they may not be able to identify themselves at all. Maybe the billing information and date of birth could help here.
I was able to call the 877 number of Hulu weeks later, at an unpopular time of the day, and the matter was sorted in a matter of minutes.
The Hulu rep on the phone, Teresa, asked me for my Hulu email address but it is unclear if the old address brought up any records. She then asked me to confirm the new email address on the account. Further, because the date of birth is immutable in the Hulu system that is what helped the representative verify my identity and in saving the day. The representative reverted the email address back to my original one.
“Your account is a cancelled account. Although your email address was changed,” said the rep, “none of your [billing] information was compromised. Hulu does not keep any credit card information on cancelled accounts, we use a different service for that.”
“It looks like you went through a different type of service anyway (PayPal) when you had signed up for Hulu using this email address.”
This was a simple close and shut case with a friendly representative who had no problem understanding the email addresses, spelled out over the phone and the overall situation.
However, countless stories have surfaced on the internet that bring to light the distress users experienced when “all the information [was] changed” from their hacked Hulu accounts.
Streaming services like Hulu should already be aware of these issues considering multiple members have shared their experiences on Hulu’s community forums:
In January 2020 alone a user named AStork posted in Hulu Community forum, “Alerting me when a new device is activated does me no good if that person took control of my account by changing the email address on the account.”
*AStork *further added, “Please send an email when the email address for the account is trying [sic] to be changed. That should be BASIC so that the owner of the account is authorizing the change, not the hacker. I couldn’t take control of my account without waiting over an hour on hold and then not knowing the gift card number that was added to pay for the subscription led to even further delays.”
Whereas others complained that their entire information had been changed, and they had to spend a considerable effort in reaching Hulu support:
“My account was completely stolen, they changed my password, my email, and my account information. The sad part is I had to Google customer service number for Hulu because you can’t get into any support options without even logging in, which I couldn’t do for my stolen account,” said user beazneez.
A spokesman from Hulu, Paul, responded within the forum, “Hey everyone! As of last fall, we now alert you via email when a new device is activated on your account.”
This idea and the original post were quickly shot down by yet another customer DeathHarb commenting in the same thread, “I’m sorry but this post is bullsh*t. They already do this. The problem is they ALLOW this to happen instead of requiring an extra verification, which was my idea which they deleted.”
Easy preventative solution
A preventative solution to situations like these that companies can implement is actually really simple: to request verification from the user via email, before the email address can be changed to another one, and to implement delays in between subsequent email changes.
For example, instead of Hulu just notifying the user that their email address was changed after it has already been changed, how about sending them a verification link which explicitly asks the user if they’d like to authorize the email change, by clicking the link? This would come in handy in the event of a compromise before any damage occurs.
Additionally, when changing email addresses, there should be a delay implemented in between subsequent requests. That means, say an attacker managed to change your email to theirs, they should not be able to change the account email a second time until at least 72 or so hours have elapsed, as an example. This would allow some time for the rightful account owner to attempt recovery.
For comparison, what happens when a Netflix account email address gets changed?
Image: Courtesy notification sent by Netflix when an account email is changed.
Unfortunately, Netflix doesn’t have the preventative security features I suggest here either. But at least they reduce the user’s dependence on telephone support by enabling contact with Netflix online and via live chat, from anywhere in the world.
Moreover, Netflix offers a proper knowledge base article educating users on mitigating this specific event when their account email is changed without permission.
Lessons learned
Incidents like these are reminders for users to enhance protections, such as using strong passwords and multi-factor authentication, where applicable. They are also motivators for companies to step up their security policies.
Steaming services are now more popular than ever, but they often trade off basic security for offering enhanced user experience, which is understandable. For example, even today Netflix and Hulu have not implemented two-factor authentication as it may cause issues with their older smart TV apps. But that is only an assumption.
When asked as to why, neither companies have responded to our request for comment.
Surely, Hulu does not let you sign up, even for a trial, without collecting billing information (PayPal or credit/debit card) which is a deterrent for casual surfers and adversaries wanting to “test drive” the Hulu platform aimlessly. And of course, collecting billing info upfront also helps with marketing and lead conversion efforts.
But, Hulu or Netflix require no re-verification of billing information or an explicit email verification sent out to the original address, during account email changes. Given such simplicity, account compromises can realistically leave users in the dark, if remediation policies around these are not properly orchestrated.
What to do when your account gets compromised?
If your account gets compromised, get in touch with Hulu or Netflix support as soon as possible with the available information ready, including your date of birth, billing details, and (if visible) the new email address set by the attacker.
With neither services offering two-factor authentication, as a general advice, users should use strong passwords, preferably generated by a password manager for their streaming service accounts, and never share the same password between any two websites. This may not totally prevent an account compromise, especially if you’re sharing your Netflix creds with a college buddy, it can still prove to be an effective deterrent strategy.
(C) 2020. Ax Sharma. All Rights Reserved.
Originally published at securityreport.com










Top comments (1)
Awesome article!