In an exclusive story reported on my blog about a month ago and on no mainstream media outlet, credentials of some 1,023 Premium accounts were found floating on the web. These user accounts belong to the popular video-on-demand streaming service, ZEE5.
The origins of the incident date back to April 12th 2020, when a new data set titled, “Zee5 Premium” (archived here) emerged on Pastebin revealing email addresses and full plaintext passwords of some Premium users. The discovery was brought to light by notifications having been sent out by the data breach monitoring service, HaveIBeenPwned, which had likely detected the newly published paste automatically, and messaged its subscribers (and only its subscribers).
Naturally, surprised to see this on HaveIBeenPwned with no public report by any news outlet, and a total lack of correspondence from ZEE5, I reached out to ZEE5's support staff on April 15th, to request them to pass these findings on to the appropriate teams so they could investigate. They were quick to respond to the support request, even during the COVID-crisis times (which is respectable), and acknowledged they had passed the findings to the "the relevant team for their review." They further added, "[We] appreciate your time & patience in the interim. We'll update you once we hear from them."
To this date, however, there's no record of an email having been sent out to impacted ZEE5 customers, advising them to change their passwords, or a public statement acknowledging the data incident. Not to forget, if this was a case of data breach (we don't know yet), ZEE5's negligence in storing passwords in plaintext, without use of any hashing or salting is problematic, if this is indeed what happened.
It is not exactly known if this was a leak, a breach, or a classic case of credential stuffing...
...that is, the party behind the set had corroborated an already-compromised set of creds. from elsewhere against ZEE5's servers in an automated fashion, and published the ones that worked. This is plausible.
But semantics don't change the importance, or seriousness of these findings.
At the very least, ZEE5 could have automatically reset passwords of the impacted accounts.
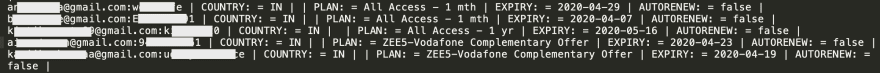
Moreover, the content of the paste is rather interesting in how it reveals the origins of the user's premium plan (e.g. promotional offers), the expiration date of the plan, along with the auto-renewal setting; almost as if it's been pulled from an API, post successful authentication.
Their authentication REST API endpoint is rather dumb simple:
https://userapi.zee5.com/v1/user/loginemail?email=FAKE@example.com&password=testttt
A failed authentication attempt returns the JSON message:
{"code":2120,"message":"The email address and password combination was wrong during login."}
Whereas, a successful login returns a beautiful token eventually granting access to the user's account:
{"token":"eyJhbGc....8IND4sZBNpMLMQ"}
In times, where APIs are increasingly falling prey to credential stuffing, there does not appear to be a hard limit on the number of requests that can be made to ZEE5's API, or any additional captcha-style security roadblocks to prevent automated login attempts.
The multi-language video streaming company claims to serve over 190 countries, with its member base exceeding a whopping 150 million, according to some sources. The company delivers video content over multiple platforms — the web, smart TVs, mobile apps, etc. One would assume an operation of this scale would take security incidents seriously.
ZEE5 falls under the corporate umbrella of massive Essel Group, the powerful conglomerate behind numerous Indian television, entertainment and news channels, and with significant ownership in Dish TV.
That does not exempt Essel or ZEE5 from the corporate responsibility of ethically catering to its customers.
My motivation behind writing this piece stems from an ethical standpoint. I believe ZEE5 users impacted by the breach must be informed that their credentials were compromised at some point, and that they should change their password - not only on ZEE5, but anywhere else they've used it. And this is something the company has not done yet, which puts both their customers and reputation at risk.
How to protect yourself?
First things first, change your ZEE5 password immediately, whether your email address appears on the list or not. You may head straight to HaveIBeenPwned to see if you’re impacted by this incident, should the list be no longer available.
If this was a case of data breach and not credential stuffing, there remains a small possibility that ZEE5 is inadvertently continuing to store even newly set passwords in plaintext. My advice in such a case is to set a strong but disposable new password and not use it on any other site. Also, remove any overly personal information from your account — and if at all possible, request your account to be deleted permanently.
Remember, also, to change your password on any other website where you’ve used the same email address and password combination, as for your ZEE5 account.
© 2020. Ax Sharma (Twitter). All Rights Reserved.
Originally published on and syndicated from Hacker Noon







Top comments (0)