PlayStation has disclosed a severe use-after-free vulnerability, after over three months since it was reported.
The vulnerability discovered by researcher Andy Nguyen exists in PS4 Firmware versions 7.02 and below. After constructing a demonstrable Proof of Concept (PoC) exploit, the researcher had responsibly reported the flaw to the company in March 2020.
If exploited in conjunction with a WebKit/Chromium vulnerability (such as CVE-2018-4386, in PS4 firmware versions up to 6.72), an attacker could:
- Achieve a fully chained remote attack on a console.
- Steal or modify user data.
- Dump and run pirated games on the console.
“Due to missing locks in option IPV6_2292PKTOPTIONS of setsockopt , it is possible to race and free the struct ip6_pktopts buffer, while it is being handled by ip6_setpktopt,” states Nguyen in the HackerOne coordinated disclosure made public yesterday.
“This structure contains pointers (ip6po_pktinfo) that can be hijacked to obtain arbitrary kernel R/W primitives. As a consequence, it is easy to have kernel code execution. This vulnerability is reachable from WebKit sandbox and is available in the latest FW, that is 7.02,” the disclosure continues.
The researcher announced more details about the vulnerability through a Twitter thread:
Here you are, https://t.co/cdVyvdqGZ6, PS4 kernel exploit for FW 7.02 and below. Vulnerability discovered on 2019-06-09.
— Andy Nguyen (@theflow0) July 6, 2020
This must be chained together with a WebKit exploit, for example https://t.co/1BYe1aFGCe for FW 6.50.
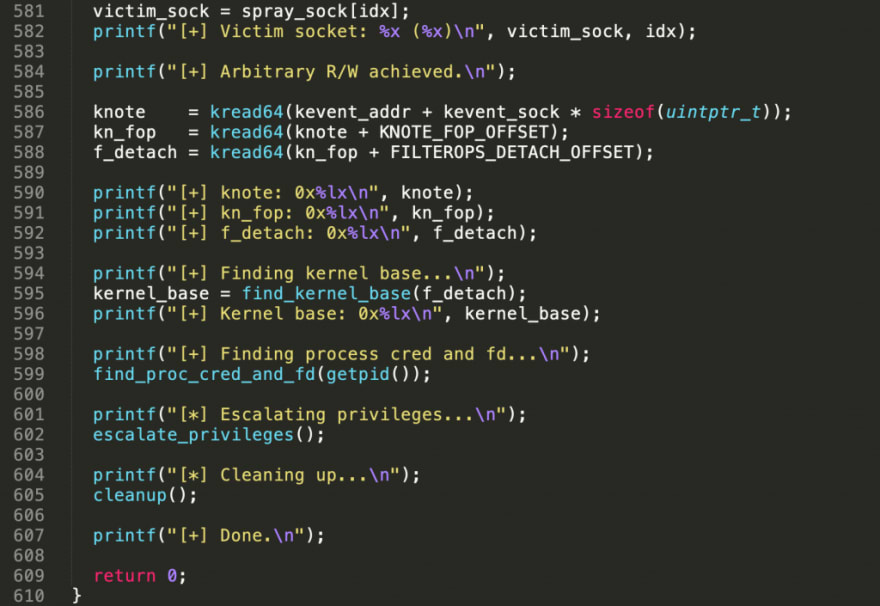
Nguyen provided a sample local privilege escalation C exploit associated with this vulnerability. It can be chained with other exploits, such as that for CVE-2018-4386) to obtain remote access.
C exploit provided by the researcher for PlayStation kernel vulnerability (Source: Security Report)
Nguyen has been awarded a $10,000 bounty award for finding and responsibly reporting this vulnerability.
As of April 22, 2020, the vulnerable devices were patched by PlayStation after rating this vulnerability as a high severity. Firmware versions 7.50 and above contain the fix released by the company.
Incidents like these are a great reminder of the times how even seemingly innocuous IoTs such as gaming consoles can become targets of attackers and potentially be abused by nation state actors. Keeping your devices up to date at all times is an advice not to be taken lightly.
Originally published on and syndicated from Security Report







Top comments (0)