Welcome back to the multi-part blog of deploying AWS security services with AWS Organizations. In Part 1 I introduced you to AWS Organizations, its prerequisites, and then configured Organizational CloudFormation StackSets. In Part 2 of our series, we went through integrating AWS GuardDuty with our AWS Organization ensuring all our accounts automatically configure and enroll into our AWS GuardDuty delegated admin account. In Part 3, we will be configuring AWS Security Hub with our AWS Organization automating the configuration and enrollment of all accounts.
Overview
Security Hub is an AWS service that delivers a comprehensive view of your security posture and gives you the ability to report, ingest, and remediate security findings in your AWS account. With it you are given a single dashboard to view the overall security posture of your environment based on many common security frameworks (CIS, PCI, etc.). Security Hub not only enables this centralized dashboard in your account, but it also enables reporting across all your AWS accounts, delivering critical security insight into your environment.
Prerequisites
AWS Security Hub is built off many AWS services for reporting your security relative to industry standards and AWS best practices. Though you do not need to initially ensure these supporting AWS services are deployed, it is recommended to plan to deploy AWS GuardDuty, AWS Inspector, and AWS Config in the near future of your enterprise AWS roll-out.
If you are wondering what is
CloudShell, read the first blog post.
The following prerequisites need to be met for this blog post:
- Full Features enabled on your AWS Organizations
- An AWS account deployed or set aside for specific use of security services
- Some basic understanding of AWS CLI
INFO: If you are using AWS Control Tower, you should use the Audit account for you Security Operations functionality. AWS highly recommends this and using the account for this functionality will better enable you to take advantage of new features in the future.
What is a SOC account? A SOC account is merely an AWS account you have set aside to conduct all security operation services (and only security operations).
WARNING: As I mentioned in Part 1 of the series, DO NOT DEPLOY your security services to the Management account if you can avoid it.
Enabling Security Hub - Management Account
The first step is to go into your Management account and enabled AWS Security Hub. If you are wondering if someone already did this you can view the services already enabled by running
aws organizations list-aws-service-access-for-organization
If the output does not have anything about securityhub.amazonaws.com you should enable it by running the following command:
aws organizations enable-aws-service-access --service-principal securityhub.amazonaws.com
INFO: If you noticed that AWS Security Hub was listed as an enabled service, you should check and see if it already is setup as a delegated admin by running aws organizations list-delegated-administrators
You can verify that Security Hub is enabled at the organizational level by re-running aws organizations list-aws-service-access-for-organization. You should see output similar to the following screenshot with Security Hub listed:
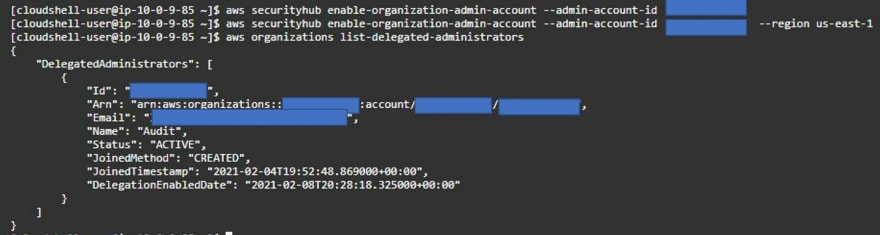
Once you have enabled the service and determined it is not already delegated, you quickly delegate to the account of your liking. As stated in Part 2, you should delegate this service to your Security Operations Center (SOC). If you are using AWS Control Tower, this account is the Audit account which is automatically created when you setup Control Tower. To delegate your Security Hub master account run the following command:
## Without specifying a region, the command will delegate the
## master account in the current region of the CloudShell
aws securityhub enable-organization-admin-account --admin-account-id 123456789123
If you need any region outside of the current region you are in, run the following command replacing the --region parameter. Example here would enable Security Hub master account on Account Id 123456789123 in us-west-2
aws securityhub enable-organization-admin-account --admin-account-id 123456789123 --region us-west-2
With delegation enabled you can verify by running aws securityhub list-organization-admin-accounts which should return similar output:
After you delegate the admin account for Security Hub, you should then enable AWS Security Hub in the Management account. You need to manually enable Security Hub within the Management account for it to automatically sync/send findings to your Security Hub administrator account. The reason for this is that the Security Hub administrator account does not have ability to configure services in the Management account. Run the following command in the Management account CloudShell to enable.
aws securityhub enable-security-hub --enable-default-standards
Again, this will enable Security Hub in the current region you have your CloudShell open in. If you are running multiple regions, you need to enable Security Hub in the Management account per region by specifying the --region parameter of the command. Once completed, you are now ready to move to configuring your Security Hub delegated administrator account.
Setting up Security Hub - Delegated Admin Account
With Security Hub administration delegated, you will need to go into the delegated administrative account known as the Security Hub administrator account (this is the account you just delegated to from the Management account). When accessing the Security Hub administrator account, you should ensure your IAM role/user has admin permissions.
INFO: If you are using AWS Control Tower, you should use the Audit account for you Security Operations functionality.
When in the account change to the primary region and open the CloudShell. Within in the CloudShell make certain to first update you have updated your AWS CLI. Easy to do this is via the one-liner I setup a GitHub project I have: AwsCloudShell. With your CloudShell updated you can enable Security Hub
With you CLI updated you can start by enabling Security Hub for the regions you want to enable. This process is identical to the last step we just did in the Management account:
aws securityhub enable-security-hub --enable-default-standards
Now that Security Hub is enabled you can configure the AWS Organizations portion of it by enabling auto-enrollment for all account within your AWS Organizations. What this will do is force all newly created accounts to enable AWS Security Hub in the region and report their findings into the Security Hub administrator account. Run the following command to enable:
## ensure you updated AWS CLI prior to running the command
aws securityhub update-organization-configuration --auto-enable
With auto-enable set, you are ready to secure your environment going forward. But what about if you already have accounts that are either reporting in by invitation or are not yet configured? We will cover that next.
Post Deployment configurations
With AWS Security Hub setup to deploy automatically leveraging AWS Organizations integration, we are all set going forward. However, for accounts deployed prior to the configuration we will need to go back in and manually Add Member similar how AWS GuardDuty worked in Part 2.
NOTE: Security Hub allows accounts to be managed outside of your AWS Organization though Invitation. Only AWS accounts that are part of the Organization can be converted from Invitation to Member accounts.
To view all the accounts for Security Hub you can see their status by going to the Security Hub web console and selecting the Accounts tab in the Settings page. You can see the status as shown below circled in red.
In the screenshot you see there are three accounts and zero of them are enrolled via Organizations or Invitation. This means I have three accounts in my Organization which could be enrolled in Security Hub and none of them are by Invitation. To add these pre-existing accounts or accounts that are of Type via Invitation you can select their checkboxes and click Add Member from the Actions menu located in the top right of the Accounts page. You will see their status turn from Not a Member to Enabling to Enabled.
With that complete all your accounts are setup and reporting into your centralized Security Hub administration account. New AWS accounts will be automatically configured and enrolled in the future.
Conclusion
As you can see the process was very similar to setting up AWS GuardDuty with Organizations regarding configurations within the Management account and within the delegated administrator account. In total you had to run about five to six commands to make this all work...and you will never need to run those commands again! AWS Security Hub is now setup for automated deployment within your Organization.
What's Next?
In Part IV of the blog series I will go over configuring AWS Config Aggregator with AWS Organizations.









Top comments (1)
May I know can we do the delegation of security hub administrator account using CloudFormation? Or for time being, there are only console, API and CLI?