Build your own penetration testing lab with AWS... or spend ton of money on various
expensivescan services.
Hello everyone!
I've decided to refuse security scan services and build a simple pentesting lab based on Kali Linux.
If you don't have an AWS account - it's the right time to create one!
EC2 and Kali Linux
Few words...
EC2 stands for Elastic Compute Cloud. In our case we'll use EC2 instance to get our Kali image installed, up and running.
Kali Linux is a Linux distribution based on Debian. It's commonly designed for penetration testing purposes, and has a lot of useful tools preinstalled.
Installation steps
- Login to your AWS account.
- On the home page, either search or select the EC2 service that is located under Compute category.
- On the EC2 Dashboard page, click the "Launch instance" instance button.
- We're looking for Kali Linux image, so, on the left sidebar, choose "AWS Marketplace", then use the search input field at the top - enter "Kali Linux" and hit the Enter/Return key on your keyboard.
- You should see the "Kali Linux" image in the search results.

- Click appropriate "Select" button.
- In the opened modal you see the description of Kali Linux and Pricing Details. Click "Continue".
- At this moment I don't care about best experience, so I choose "t2.micro" just because free tier eligible. Choose the instance type and click "Review and Launch". Clicking the "Review and Launch" button will redirect us to the last step. AWS has some default configuration setup for storage, tags, security groups etc. You can edit those configs if you want.
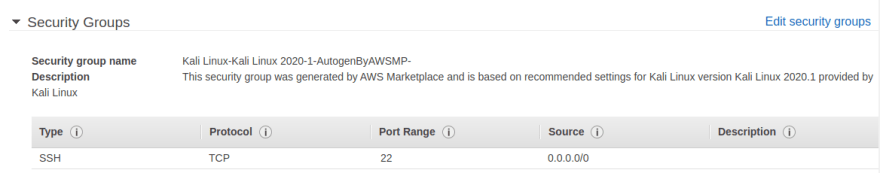
- On "Step 7: Review Instance Launch" page you can review your instance configuration. Please make sure your security group allows SSH.
- Click the "Launch" button.
- In the opened modal select the "Create a new key pair" option in the dropdown field, enter a key pair name (e.g. kalilinux), and click the "Download Key Pair" button.

- Please make sure you have downloaded the key pair file, and click the "Launch instance" button.
That's all! Few moments later you should see new running ec2 instance - just click the "Instances" link in left menu.
What's next?
In the next post I want to explore the power of OWASP ZAP and investigate to see how can I setup and automate some scans to prevent vulnerabilities. And of course, with beautiful reports and notifications...
If you have an idea that could help me in my research, please share in the comments. Thanks! :)







Top comments (3)
Great article on building your own penetration testing lab! For those who need help setting up or running their lab, there are many reputable penetration testing companies that can offer assistance. Be sure to do your research and choose a company with a good track record and experience.
Ey! I'm waiting the next post!
Published :)