The other day I was stoked when I got to use Argo Tunnels, it’s a neat piece of software that builds a bridge to the internet from your local machine, I wrote about it a few days back Argo Tunnels are fun!
The problem with me is I have interest-based learning, if the project doesn't interest me I won't be able to go ahead with it. So I decided to update my portfolio! but using Continuous deployment, podman and Argo tunnels!
Things you'll get experience with in this post:
- Gitlab Runner Setup using podman
- Cloudflared tunnel setup using systemd
- Continuous deployment using Gitlab CI/CD using containers!!
- Running a completely rootless setup
Let’s get started with cloudflared installation and setup.
Before starting please make sure you go through the following
As of now you need a domain name and you need to change the nameservers to that of Cloudflare, which is a bit irritating to do in case you cannot afford a domain name or you do not wish to use their nameservers. I hope they remove this dependency in the future.
Firstly head over to the Downloads section and choose a method you're comfortable with.
I'm using Rocky Linux, so I downloaded the amd64 / x86-64 RPM
$ wget https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-x86_64.rpm
If you do not have wget installed you can do so on Centos/Rocky Linux using
$ sudo yum install -y wget
or
$ sudo dnf install -y wget
For alternate ways of downloading a file check this link
One can also install cloudflared by downloading it directly from the Github releases page, which is the most up-to-date place to download from.
To create a tunnel follow the docs
If you run the following it will create a global systemd service, which is not something I want.
cloudflared --config config.yaml service install
Read the following on how to create a Tunnel
I created the config in my user directory as such
.cloudflared/config.yml
tunnel: Tunnel ID
credentials-file: /home/leon/.cloudflared/TunnelID.json
ingress:
- hostname: leonnunes.dev
service: http://localhost:8080
#Catch-all rule, which just responds with 404 if traffic doesn't match any of
# # the earlier rules
- service: http_status:404
It will copy this to the system folders /etc/cloudflared/cloudflared-config.yaml and create the relevant systemd config.
One can create the following in ~/.config/systemd/user/cloudflared.service
[Unit]
Description=Argo Tunnel
After=network.target
[Service]
TimeoutStartSec=0
Type=notify
ExecStart=/usr/bin/cloudflared --config /home/leon/.cloudflared/config.yml --no-autoupdate tunnel run
Restart=on-failure
RestartSec=5s
[Install]
WantedBy=multi-user.target default.target
Then use
systemctl --user daemon-reload
and
systemctl --user enable --now cloudflared.service
To check if this is running run
systemctl --user status cloudflared.service
cloudflared.service - Argo Tunnel
Loaded: loaded (/home/leon/.config/systemd/user/cloudflared.service; enabled; vendor preset: enabled)
Active: active (running) since Thu 2021-09-30 12:26:47 IST; 8min ago
Main PID: 4689 (cloudflared)
CGroup: /user.slice/user-1000.slice/user@1000.service/cloudflared.service
└─4689 /usr/bin/cloudflared --config /home/leon/.cloudflared/config.yml --no-autoupdate tunnel run
Sep 30 12:26:46 rk-minikube cloudflared[4689]: 2021-09-30T06:56:46Z INF Settings:
That's it for the Cloudflared setup.
Now let’s set up the Gitlab runner using podman.
The Gitlab docker documentation gives you an overview, this is what I did
# Create a volume gitlab-test
$ podman volume create gitlab-test
# Register the gitlab runner
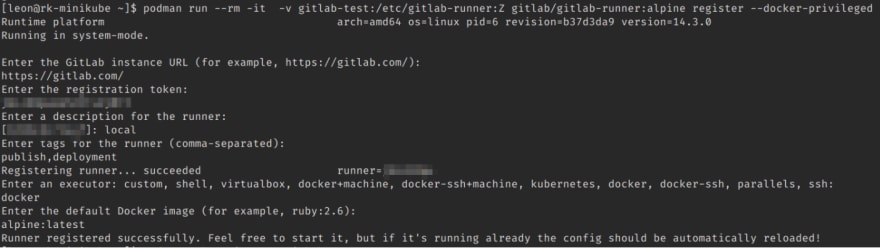
$ podman run --rm -it -v gitlab-test:/etc/gitlab-runner:Z gitlab/gitlab-runner:alpine register --docker-privileged
# I had to give the `--docker-privileged` flag without that it wouldn't let me connect to the docker socket.
Time to start the gitlab runner
$ podman run -dit --security-opt label=disable --name gitlab-runner-priv -v /run/user/1000/podman/podman.sock:/var/run/docker.sock -v gitlab-runner-config:/etc/gitlab-runner:Z gitlab/gitlab-runner:alpine
Important Notes(Security):
- Mounting the podman socket, is the equivalent of giving full access to the containers under that user. From a security standpoint this is dangerous so please use a locked-down environment and not a public environment.
- --security-opt label=disable means SELinux labelling won't happen, in other words, if you do not do this SELinux will complain that your container isn't supposed to access the podman socket.
If you want to start the GitLab runner on boot you can do this.
# change directory to the user.
$ cd ~
$ podman generate systemd gitlab-runner-priv| tee .config/systemd/user/gitlab-runner.service
# Enable on boot
$ systemctl --user enable --now gitlab-runner.service
After a lot of procrastination, I was able to complete this much, stay tuned for part 2 in which I will deploy the Gitlab CI/CD pipeline.






Top comments (0)